DragonForce Ransomware Targets 363 Companies with Cart
Active since December 2023, DragonForce has solidified its position as a formidable entity within the cybercrime landscape. Operating under a sophisticated Ransomware-as-a-Service (RaaS) model, the...
Active since December 2023, DragonForce has solidified its position as a formidable entity within the cybercrime landscape.
Operating under a sophisticated Ransomware-as-a-Service (RaaS) model, the group aggressively brands itself as a “cartel” to consolidate power and influence.
This strategic positioning allows them to attract a wide network of affiliates while distinguishing their operations from standard criminal enterprises.
Their rise has been marked by a steady evolution in tactics, making them a persistent threat to global organizations.
To support their expansion, DragonForce utilizes prominent dark web forums such as BreachForums, RAMP, and Exploit for recruitment and promotion.
They differentiate their services by offering unique tools like “RansomBay,” which facilitates customized payload generation, and specialized harassment calling services to pressure victims.
These operational vectors are designed to maximize the psychological and financial impact on targeted entities, ensuring higher payment success rates.
By providing data analysis support and team coordination tools, they offer a comprehensive suite that rivals established legitimate software enterprises.
Following their initial emergence, S2W analysts identified that the group targeted 363 companies between December 2023 and January 2026.
The frequency of these attacks has shown a consistent upward trajectory, peaking in December 2025 with 35 victims published in a single month.
This data highlights the group’s growing operational capacity and their intent to scale attacks against a broader range of industries.

Beyond standard attacks, DragonForce has actively engaged in adversarial relationships with rival ransomware groups, occasionally launching infrastructure-level attacks against competitors.
Conversely, they have also sought alliances to strengthen their ecosystem position. This complex web of interactions demonstrates their ambition to not just participate in the market, but to dominate the RaaS economy through both cooperation and conflict.
Technical Analysis of Windows Binaries
Recent technical assessments of the DragonForce Windows binaries reveal that while the core encryption routines and process termination methods remain consistent, significant structural updates have been introduced.
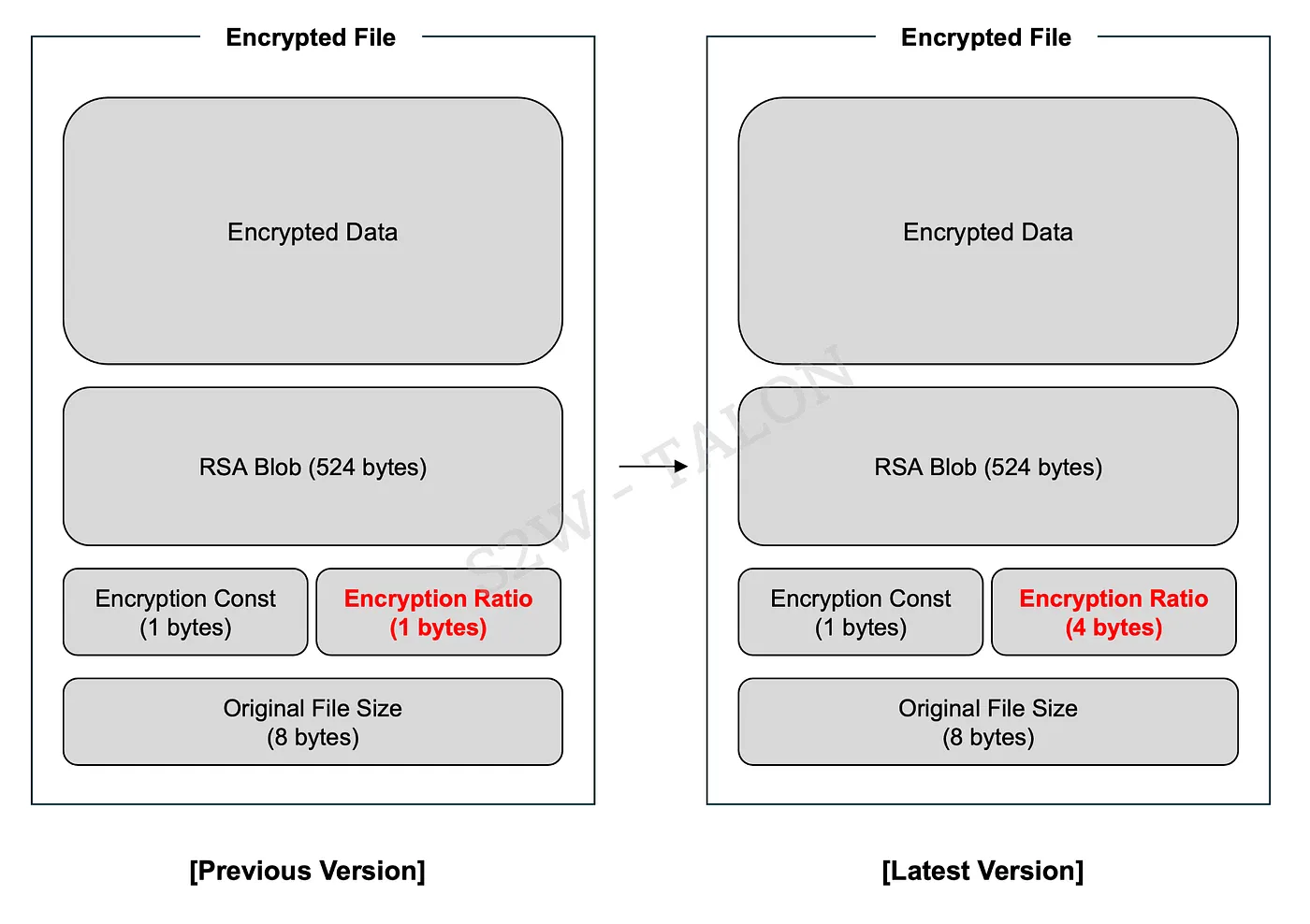
The ransomware continues to employ the Bring Your Own Vulnerable Driver (BYOVD) technique to neutralize security processes, ensuring successful encryption. However, the metadata structure appended to encrypted files has undergone modification.
The “Encryption Ratio” field was expanded from one byte to four bytes, increasing the total metadata size to 537 bytes.
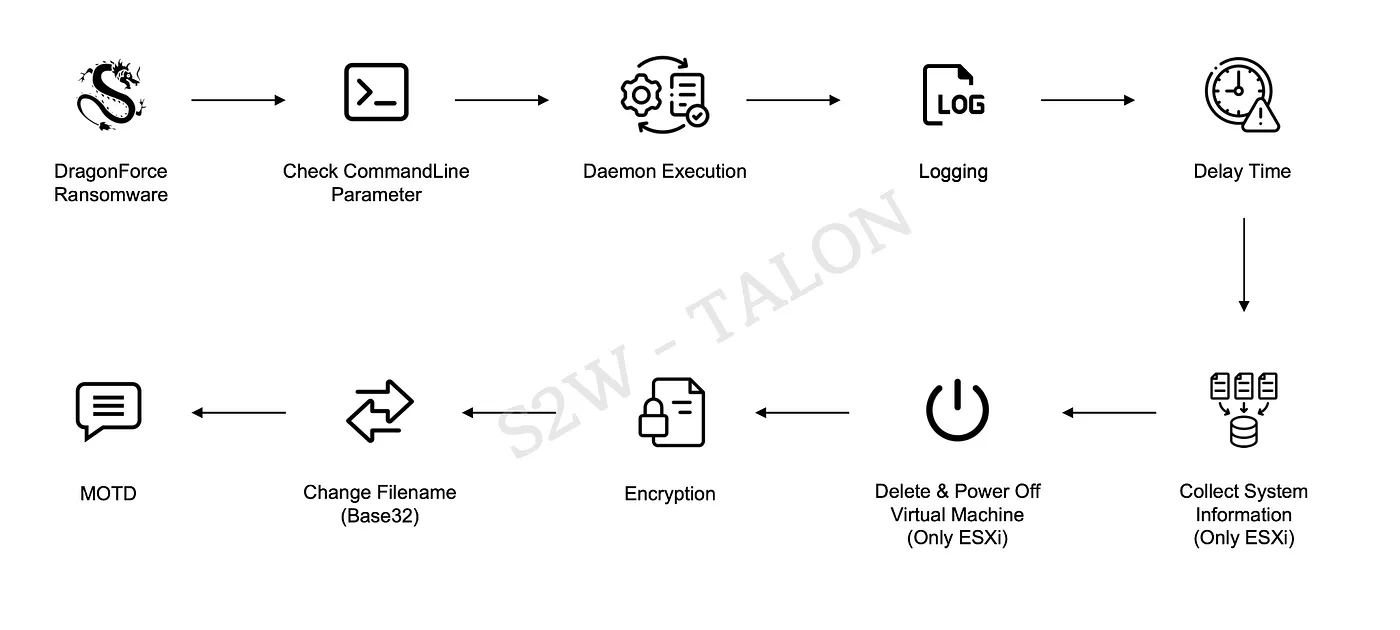
Additionally, the latest builder version includes a beta feature called “encryption_rules,” which allows operators to override encryption modes for specific file extensions.
If no specific rule is defined, the malware applies full, partial, or header-based encryption based on the file size.
Upon execution, the ransomware decrypts its embedded configuration using the ChaCha8 algorithm before initiating these routines.
This new configuration option grants attackers precise control over how different data types are impacted, optimizing the speed and severity of the encryption process based on the victim’s environment.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.