Muddled Libra Rogue VM Attacks VMware vSphere: Key T
During a September 2025 incident response, investigators identified a rogue virtual machine operating within a VMware vSphere environment, linking it with high confidence to Muddled Libra, an...
During a September 2025 incident response, investigators identified a rogue virtual machine operating within a VMware vSphere environment, linking it with high confidence to Muddled Libra, an adversary also tracked as Scattered Spider and UNC3944.
The VM acted like a quiet staging host, giving the intruders a place to recon the network, pull down tools, and move toward data theft; it also showed how a single VM can become a bridge between identity systems and cloud services during an intrusion in plain sight.
The group is known for social engineering such as smishing and vishing, and for impersonating employees to push help desks into password or multi-factor resets.

It also tends to avoid heavy malware, leaning on legitimate admin utilities and the victim’s own infrastructure to blend in.
Palo Alto researchers identified attackers accessed vSphere about two hours after initial access and created a new VM named “New Virtual Machine.”
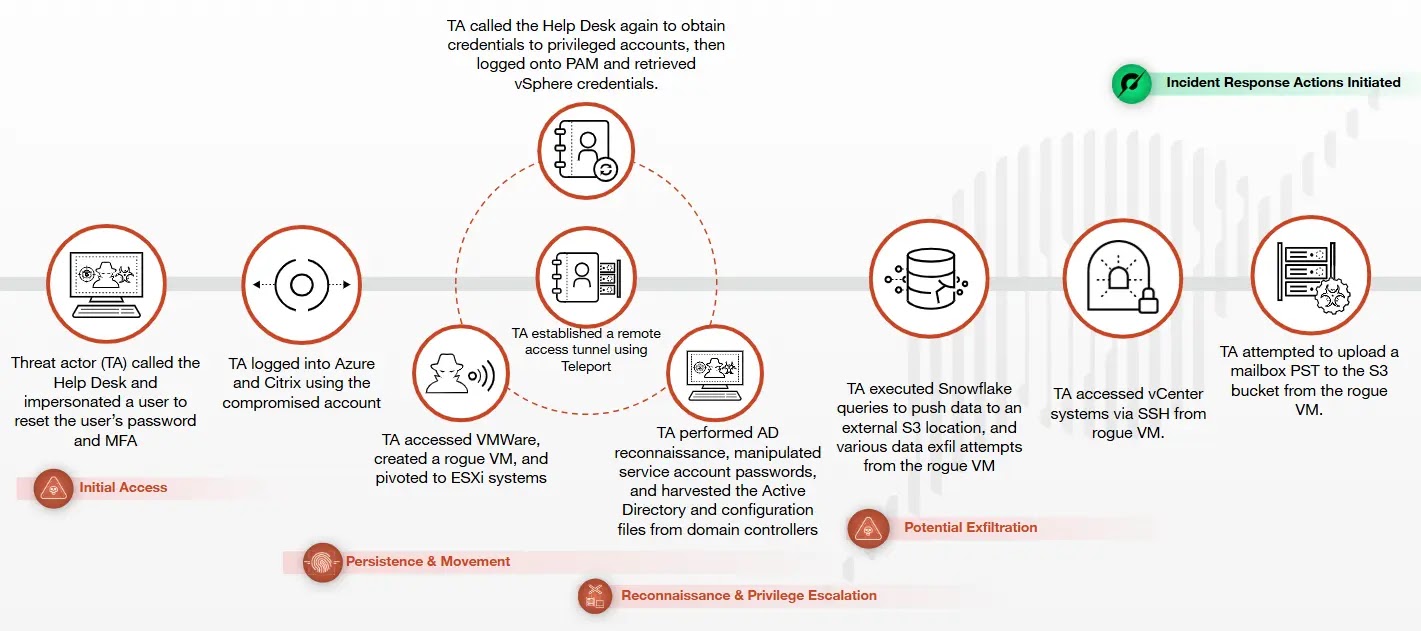
Soon after logging in, they pulled stolen certificates and used them to forge tickets as they expanded control.
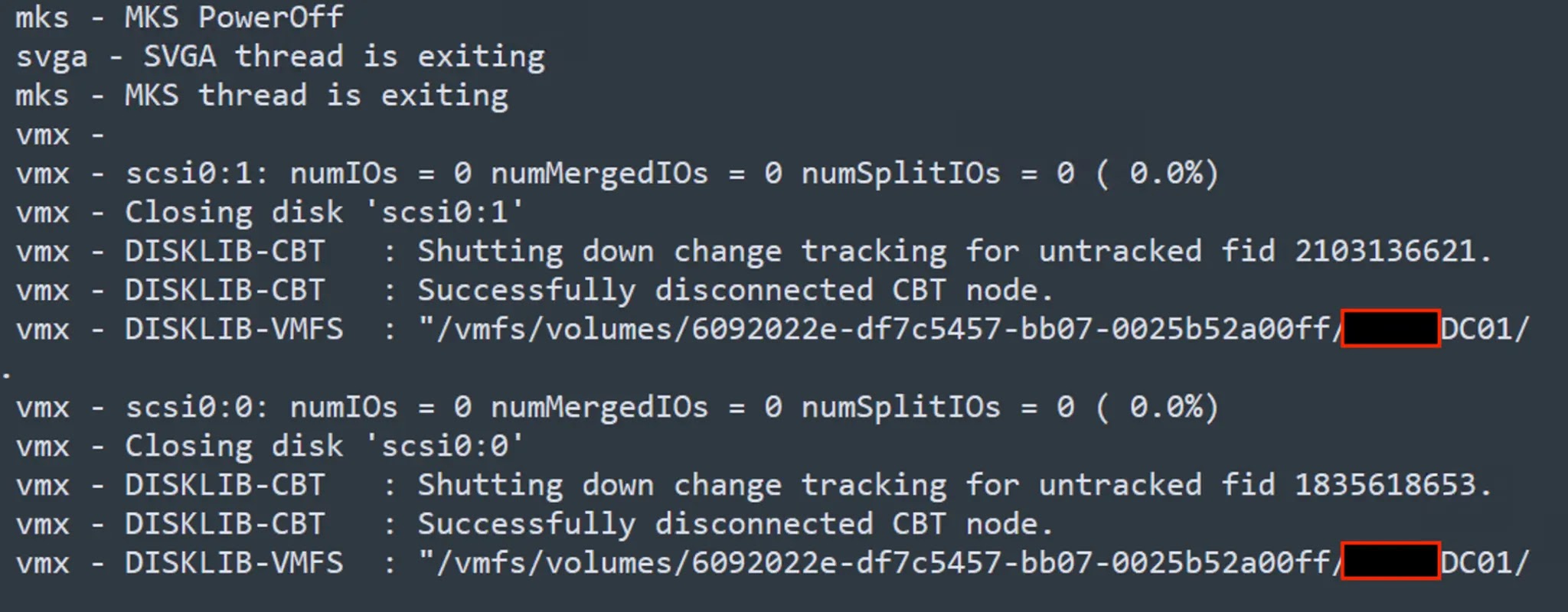
From that foothold, the intruders powered down virtualized domain controllers, mounted their VMDKs, and copied NTDS.dit and SYSTEM to the VM.
They then ran directory discovery with ADRecon and reviewed service principal names, while also reaching into the victim’s Snowflake environment and later trying to move mailbox data, including a PST, off-network using file-sharing sites and S3 Browser..
Chisel tunnel persistence
Within minutes of building the rogue VM, the attackers set up persistence using an SSH tunnel with Chisel, delivered in a ZIP named goon.zip from an attacker-controlled AWS S3 bucket.
Network logs showed traffic to an attacker-controlled address over TCP 443 that continued for roughly 15 hours, helping the tunnel look like normal HTTPS.
Defenders can reduce risk by tightening identity controls, enforcing least privilege for vSphere and admin accounts, and watching for suspicious VM creation, DC power-off events, and unexpected VMDK mounts.
Continuous monitoring for unusual use of common tools, odd outbound 443 from newly created systems, and anomalous access to cloud data platforms can help catch this living-off-the-land approach before it turns into broad lateral movement and theft.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.