RecoverIt Exploits Windows Service Recovery to Execute Payload
“RecoverIt,” a new open-source offensive security tool, has been released, enabling Red Teamers and penetration testers to establish persistence and execute lateral movement on compromised Windows...
“RecoverIt,” a new open-source offensive security tool, has been released, enabling Red Teamers and penetration testers to establish persistence and execute lateral movement on compromised Windows systems through a novel method.
The tool, developed by security researcher TwoSevenOneT, weaponizes the built-in failure recovery mechanism of Windows Services to trigger arbitrary code execution, bypassing some of the most common detection heuristics used by Endpoint Detection and Response (EDR) systems.
Windows Services are designed with resilience in mind. The Service Control Manager (SCM) includes a “Recovery” tab for each service, allowing system administrators to define specific actions if a service fails unexpectedly.
These actions typically include restarting the service, restarting the computer, or, most critically for this exploit, running a specific program.
RecoverIt abuses this functionality by programmatically modifying a service’s configuration to execute a malicious payload instead of a legitimate recovery tool.
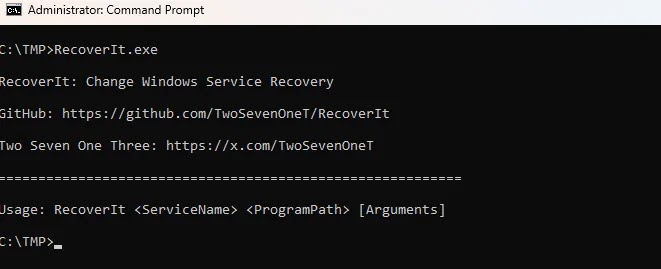
The tool operates by taking three simple arguments: the target service name, the program to execute upon failure, and the parameters for that program.
Windows Service Failure Recovery Functions Exploited
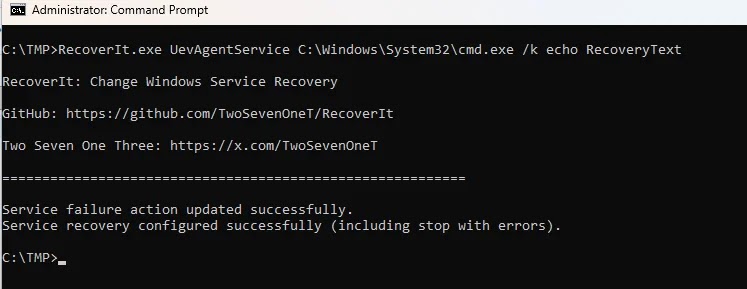
In the documentation accompanying the release, the security researcher TwoSevenOneT highlights a specific scenario involving the “UevAgentService” (User Experience Virtualization Agent).
Research revealed that this service is prone to crashing immediately upon execution if the broader UE-V service is disabled on the host machine.
By targeting an unstable service like UevAgentService, an attacker can create a reliable trigger mechanism. The attacker uses RecoverIt to configure the service so that when the inevitable crash occurs, the Windows Service Control Manager (services.exe) automatically executes the defined payload such as a Command Prompt (cmd.exe) or a Cobalt Strike beacon.
Because the execution is spawned directly by services.exe as a recovery action, it blends in with legitimate system background activity, potentially masking the malicious intent from casual observation.
The release of RecoverIt highlights a shift in evasion tactics. Traditionally, attackers seeking persistence via Windows Services have focused on modifying the ImagePath (or binPath) the registry value that tells Windows which executable to run when starting a service.
However, because this is a well-known attack vector, SysAdmins and EDR solutions now monitor it ImagePath extensively for unauthorized changes or suspicious binaries.
RecoverIt circumvents this scrutiny entirely. It leaves the legitimate ImagePath untouched. Instead, it modifies the FailureCommand and FailureActions configurations. As noted in the tool’s summary, “SysAdmins tend to focus more on the ImagePath of services,” leaving the recovery settings as a blind spot in many defensive postures.
While the execution method is stealthy, it is not invisible. The primary challenge for defenders is that the malicious payload execution is not explicitly detailed in the standard service crash event logs.
As shown in the researcher’s findings, the Windows Event Log records service failures (e.g., UevAgentService terminating unexpectedly) but does not necessarily log the program that the recovery handler subsequently launched in the same event entry.
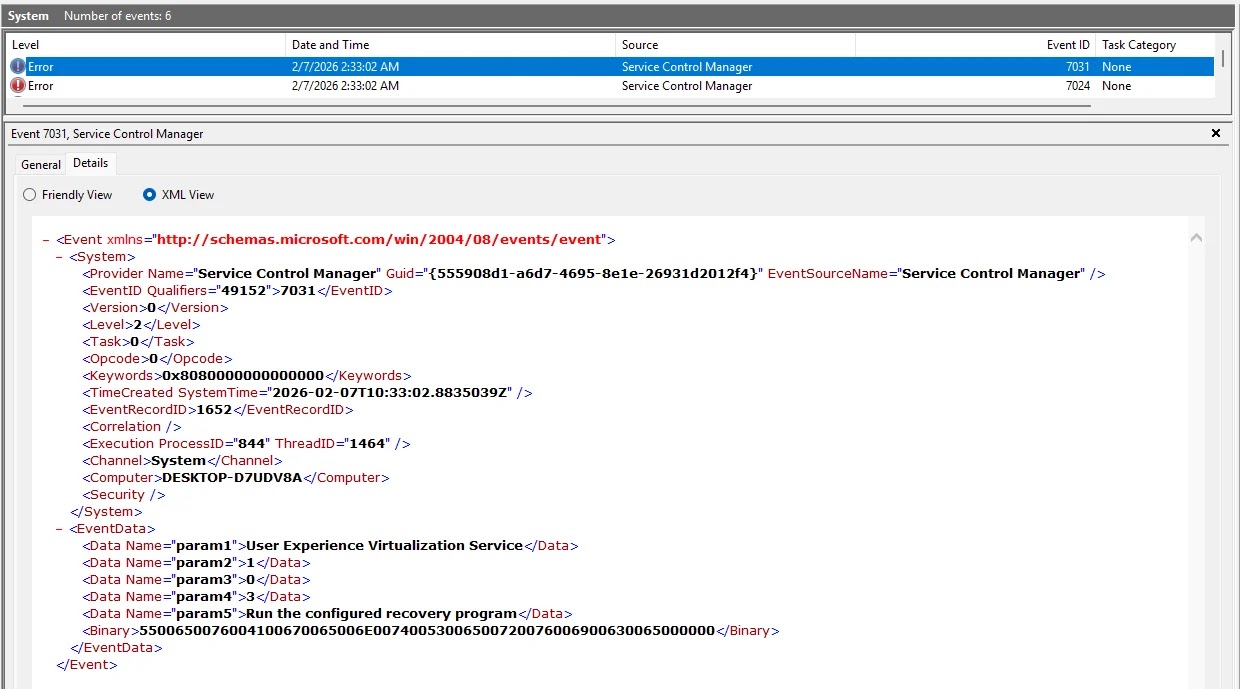
To detect this technique, security teams must broaden their monitoring scope. Detection logic should be updated to alert on changes to service recovery configurations, specifically monitoring for modifications to FailureCommand and FailureActions registry keys.
Furthermore, process monitoring should scrutinize child processes spawned by services.exe that correlate with service failure events, particularly if those child processes are command interpreters like PowerShell or CMD.
The release of RecoverIt serves as a reminder that legitimate system administration features often provide the most effective camouflage for attackers, necessitating a defense-in-depth approach that looks beyond standard indicators of compromise.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.