Bulletproof Hosting Leverages ISPsystem Servers for Cyber
The evolving landscape of online threats reveals a new tactic: cybercriminals are now strengthening their attacks by concealing them behind legitimate technology. Late in 2025, a series of ransomware...
The evolving landscape of online threats reveals a new tactic: cybercriminals are now strengthening their attacks by concealing them behind legitimate technology.
Late in 2025, a series of ransomware incidents revealed that attackers were using virtual machines provisioned through ISPsystem, a popular platform used by hosting companies to manage their servers.
By renting these virtual computers, criminals gained access to powerful infrastructure that appeared trustworthy, allowing them to launch attacks without triggering immediate alarms.
This abuse of commercial infrastructure highlights a growing sophistication in how threat actors procure their resources, shifting from compromised home computers to high-bandwidth data center assets.
These virtual machines became the launchpad for some of the most dangerous ransomware variants, including WantToCry, LockBit, and BlackCat.
The attackers utilized these servers to establish remote connections, distribute malicious software, and control infected networks from a safe distance.
Since the servers were hosted on legitimate networks, they bypassed many standard security blocks that typically flag suspicious traffic.
This method provided a stable and reliable base of operations, making it difficult for defenders to shut them down quickly.
The integration of commodity malware delivery mechanisms further complicates the defensive posture for affected organizations, requiring more advanced detection strategies.
Sophos analysts noted this malicious activity after observing a distinct pattern in the network identifiers of the attacking machines.
They discovered that thousands of these servers shared the exact same computer names, derived from the hosting software’s default templates.
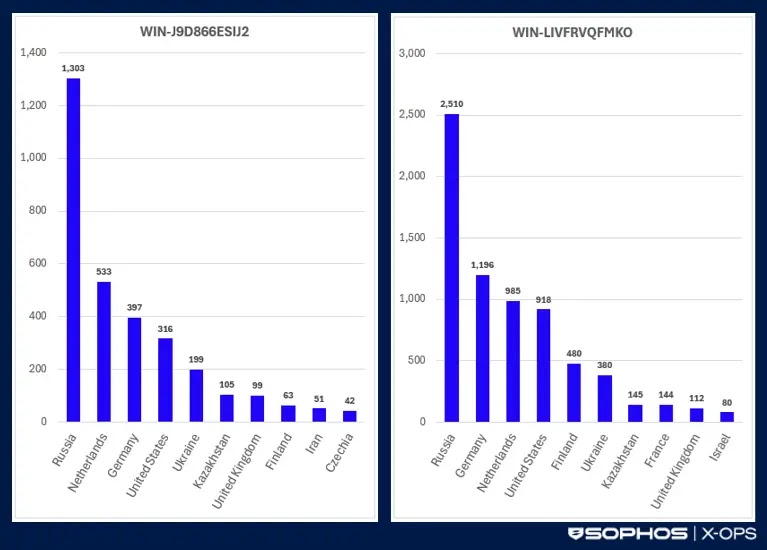
This oversight allowed researchers to trace the widespread infrastructure, identifying over 3,000 active devices in regions including Russia, Europe, and the United States.
The sheer volume of these machines suggests a highly organized effort to maintain a resilient network for criminal operations.
Exploiting Static Configuration Templates
The persistence of this threat relies heavily on how these virtual environments are sold.
Service providers like “MasterRDP,” operating as rdp.monster, have built a business model around selling these pre-configured servers.
They market these services on underground forums as “bulletproof,” promising that the servers will remain online despite abuse reports.
These providers act as a critical supply chain link, offering affordable access to dedicated hardware that facilitates large-scale malicious campaigns.
By purchasing these resources, attackers can bypass the complex technical challenges of building their own botnets.

The technical mechanism enabling this scale is the use of static templates within the VMmanager software.
When a new virtual machine is set up using these default templates, it retains specific system identifiers instead of creating unique ones.
This lack of randomization means that every server spawned from the same template looks identical at a system level.
This feature simplifies management for legitimate administrators but inadvertently provided cybercriminals with a standardized, mass-produced fleet of attack servers ready for immediate deployment.
Recommendations include avoiding default templates and implementing stricter randomization protocols to prevent such uniform exploitation.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.