ShadowSyndicate Uses Server Transition in Ransomware
ShadowSyndicate, a malicious activity cluster first identified in 2022, has evolved its infrastructure management techniques by adopting a server transition method that allows the threat actor to...
ShadowSyndicate, a malicious activity cluster first identified in 2022, has evolved its infrastructure management techniques by adopting a server transition method that allows the threat actor to rotate SSH keys across multiple servers.
This new approach makes it harder for security teams to track the group’s operations.
The threat actor initially gained attention for using a single SSH fingerprint (1ca4cbac895fc3bd12417b77fc6ed31d) across numerous malicious servers, creating a traceable pattern that researchers could follow.
The campaign represents a significant shift in how cybercriminals manage their attack infrastructure.
ShadowSyndicate operates by reusing previously employed servers and sometimes rotating various SSH keys across their infrastructure.
When performed correctly, this transition appears legitimate, as if a server has been transferred to a new user. However, operational security mistakes have allowed security teams to identify these connections.
Group-IB analysts identified two additional SSH fingerprints (ddd9ca54c1309cde578062cba965571e and 55c658703c07d6344e325ea26cf96c3b) that exhibit similar behavioral patterns to the original fingerprint.
These discoveries came after Intrinsec researchers reported another SSH fingerprint in 2025, prompting deeper investigation into the threat actor’s evolving tactics.
Infrastructure and Attack Frameworks
The newly discovered infrastructure reveals connections to at least 20 servers functioning as command-and-control centers for different attack frameworks.
Analysis shows that ShadowSyndicate continues deploying familiar toolkits including Cobalt Strike, MetaSploit, Havoc, Mythic, Sliver, AsyncRAT, MeshAgent, and Brute Ratel.
These frameworks enable the group to maintain persistent access to compromised networks and deploy ransomware payloads.
Each discovered SSH fingerprint forms distinct clusters of servers that share similar characteristics.
Further examination of related IP addresses reveals connections to various ransomware groups including Cl0p, ALPHV/BlackCat, Black Basta, Ryuk, and Malsmoke.
This pattern suggests that ShadowSyndicate may operate either as an Initial Access Broker or provide bulletproof hosting services to cybercriminals.
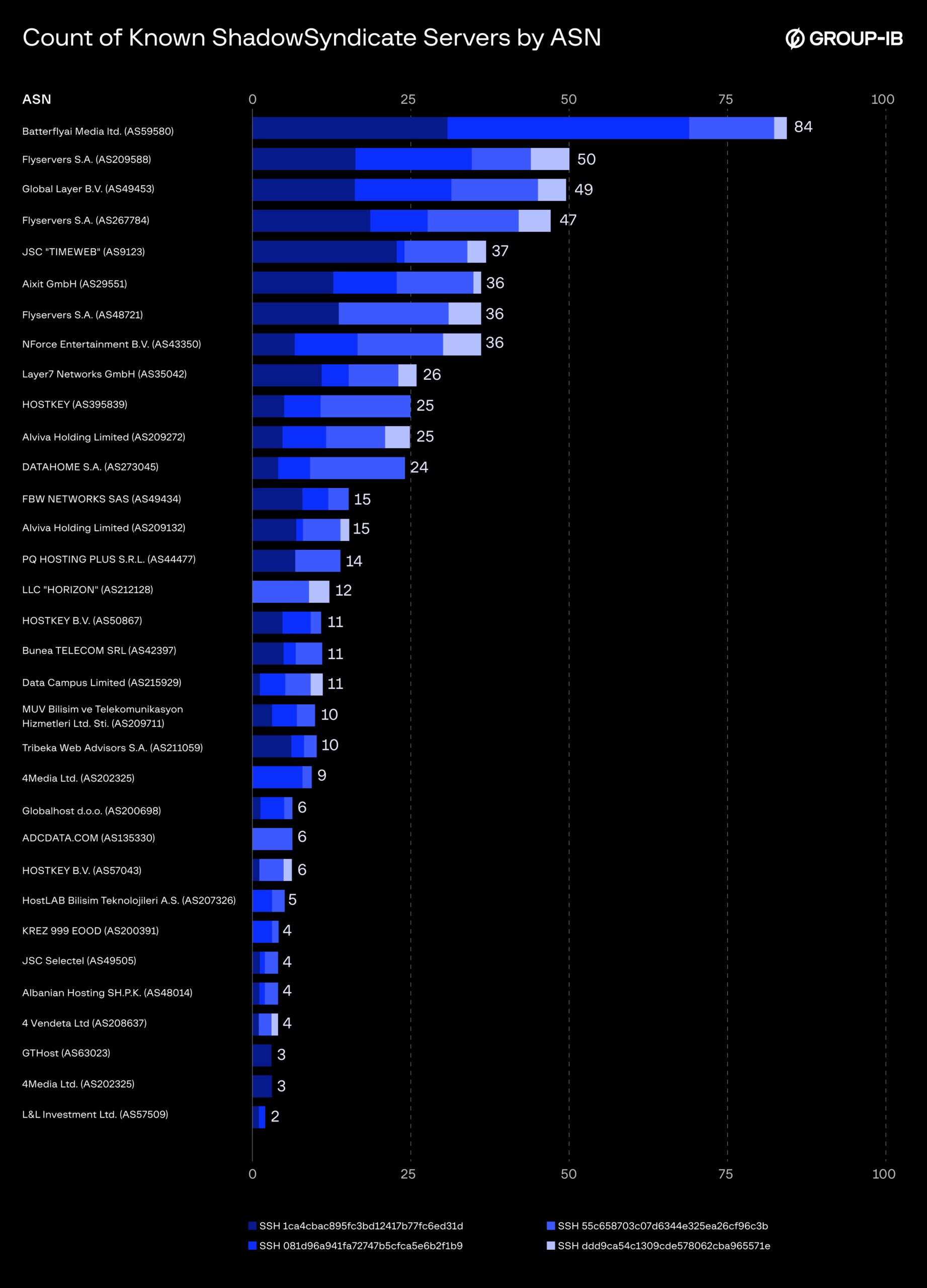
The threat actor demonstrates consistent preferences for specific hosting providers across all discovered clusters.
While these servers have different owners and originate from various territories, the alignment with familiar autonomous system numbers creates predictable patterns useful for infrastructure correlation and proactive detection.
Organizations should incorporate indicators of compromise into their threat intelligence platforms and monitor activity related to IP addresses within frequently used autonomous systems.
Security teams should watch for repeated multifactor authentication failures, high volumes of login attempts, and rapid authentication attempts with valid credentials.
Additionally, monitoring unusual login source locations and mismatches between login attempts and device locations receiving authentication prompts can help detect compromise attempts.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.