DragonForce Ransomware Attacks Critical Business Data Exfiltration
Since its appearance in late 2023, a new ransomware operation dubbed DragonForce has become a significant threat to organizations globally. This sophisticated malware campaign targets critical...
Since its appearance in late 2023, a new ransomware operation dubbed DragonForce has become a significant threat to organizations globally.
This sophisticated malware campaign targets critical business infrastructure across multiple industries, using advanced techniques to encrypt files and steal sensitive corporate data.
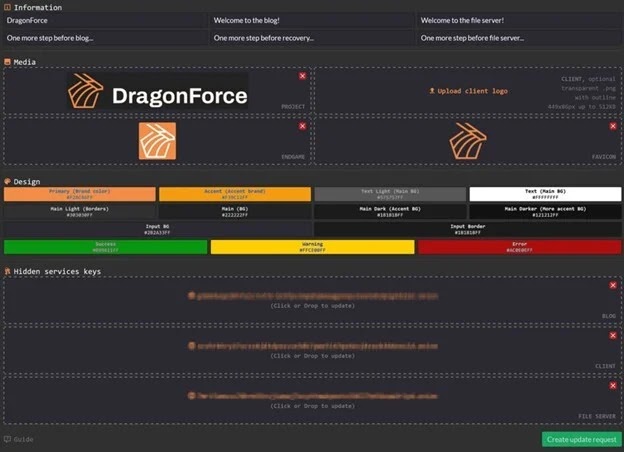
The group operates on a ransomware-as-a-service model, offering cybercriminal affiliates a comprehensive toolkit to launch devastating attacks against victims.
DragonForce employs what researchers call a dual-extortion strategy. This means the attackers not only encrypt valuable business data, making it inaccessible to the organization, but also secretly copy and steal sensitive information before the encryption occurs.
The stolen data becomes leverage for extortion, as the attackers threaten to publish it on dark web leak sites unless the ransom is paid.
This approach significantly increases pressure on victims who might otherwise restore from backups.

The ransomware has particularly focused on manufacturing, business services, technology, and construction sectors. Organizations in the United States, United Kingdom, Germany, Australia, and Italy have experienced the highest concentration of attacks.
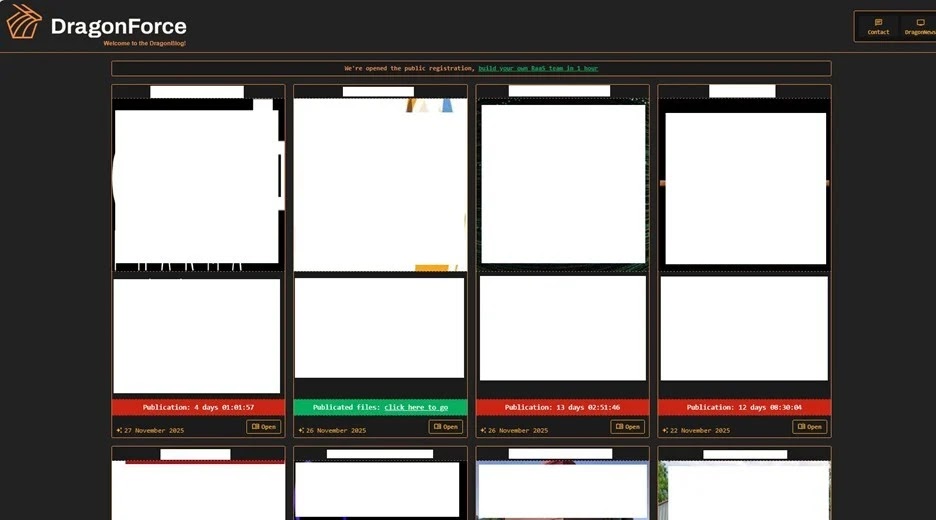
LevelBlue analysts identified that DragonForce demonstrates remarkable adaptability by continuously refining its operational tools and techniques, evolving from using dedicated victim sites to maintaining a centralized domain for hosting leaked data.
What makes DragonForce especially dangerous is its multi-platform capability.
The malware can attack Windows, Linux, ESXi, BSD, and NAS systems, providing affiliates with extensive reach across different computing environments.
The service supports various encryption modes including full, header, and partial encryption, along with customizable options for individual files and delayed-start features for launching attacks at specific times.
Technical Capabilities and Infection Methods
The ransomware’s technical sophistication sets it apart from many other threats. DragonForce includes multithreading capabilities to improve encryption performance and detailed logging to track the encryption process.
One notable feature allows affiliates to perform dry runs without actual encryption, essentially testing the attack before deployment.
The group provides unlimited storage with dedicated infrastructure monitored continuously, offering free partner services including professional file analysis and decryption support.
During execution, DragonForce performs network reconnaissance by scanning SMB ports within IP ranges to identify vulnerable systems.
It uses a mutex identifier originally documented in samples derived from leaked Conti ransomware source code, demonstrating code reuse from previous malware families.
The ransomware also deletes volume shadow copies using Windows Management Instrumentation Command-line (WMIC) commands, specifically “wmic.exe shadowcopy where ID delete,” preventing victims from recovering files from backup snapshots.
Security experts recommend organizations follow specific defensive measures against DragonForce. Implement multifactor authentication across all systems and maintain rigorous patch management to close vulnerabilities.
Organizations should regularly back up files following a documented backup process, as restoration from backups remains the fastest recovery method.
Additionally, enable advanced endpoint detection capabilities, anti-ransomware protection with shadow copy preservation, and application control to prevent unauthorized execution.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.