Beware of Weaponized Voicemail Messages that Allows Hackers to
Cybercriminals are actively changing their approach, increasingly relying on social engineering tactics. This strategic shift enables them to bypass traditional security defenses, often leaving many...
Cybercriminals are actively changing their approach, increasingly relying on social engineering tactics. This strategic shift enables them to bypass traditional security defenses, often leaving many users vulnerable and unprepared.
A sophisticated new campaign dubbed “Voicemail Trap” explicitly targets users with fake voicemail notifications designed to look like routine business communications.
These messages often appear to come from trusted financial entities and use convincing German-language lures to trick victims into engaging with malicious content.
The attack relies heavily on manipulating user trust rather than leveraging complex software exploits.
The attack sequence begins when a target receives a notification claiming they have an urgent new voice message waiting.
Clicking the provided link directs them to a compromised website hosted on a bank-themed subdomain, which lends an air of legitimacy to the scam.
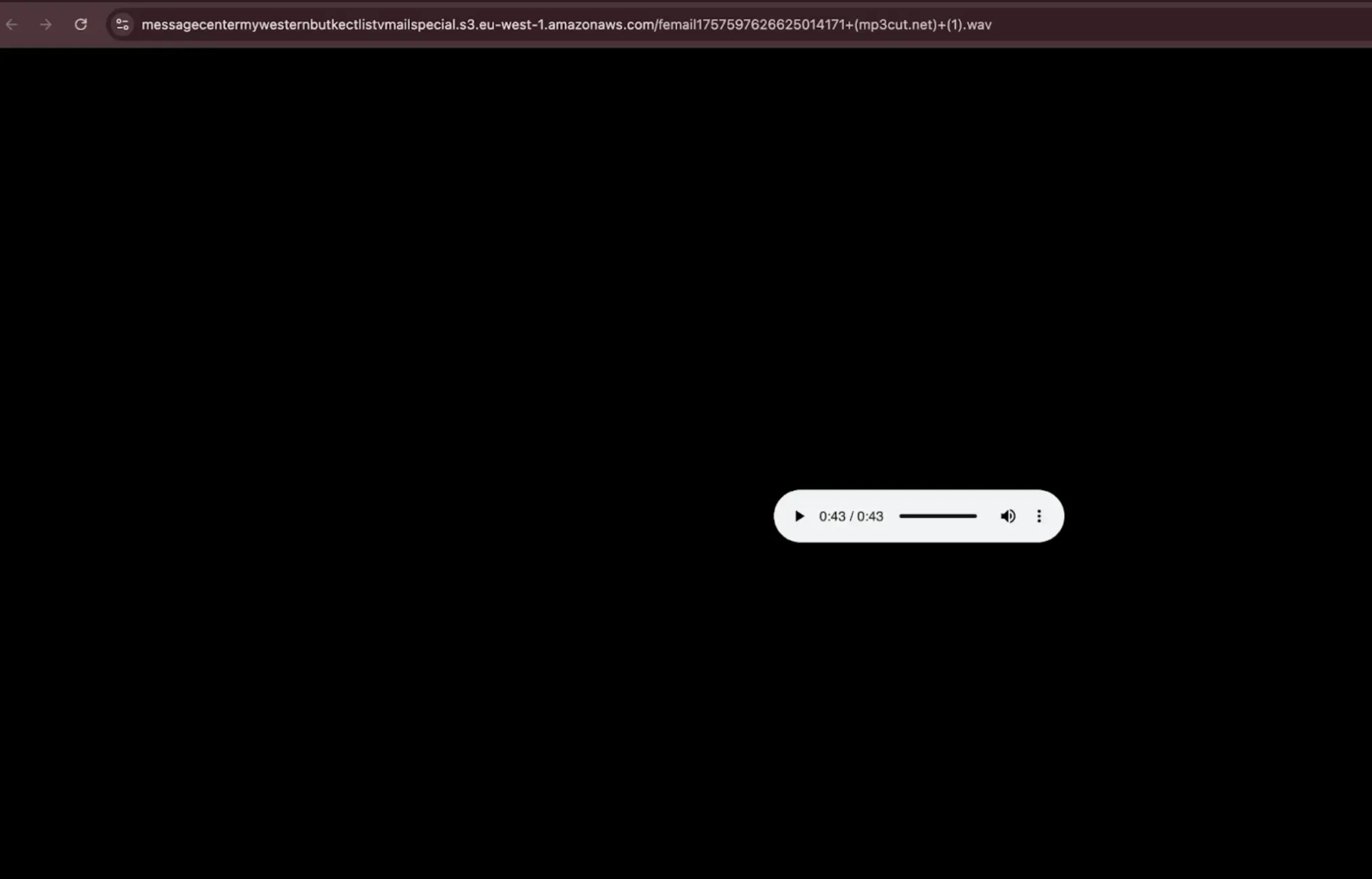
The landing page mimics a standard audio player interface and prompts the user to listen to the recording.
However, instead of playing an audio file directly, the site instructs the user to download a specific script to hear the message.
Censys researchers identified this emerging threat on January 12, 2026, observing eighty-six distinct web properties delivering these malicious lures.
The downloaded file is actually a Windows Batch (BAT) script disguised as a necessary audio codec update or media component.
Once the user manually executes this script, it initiates a multi-stage infection process that ultimately compromises the victim’s device, often without triggering standard antivirus alarms due to the use of legitimate administrative tools.
Deceptive Infection and Persistence Mechanism
The core of this attack lies in its clever ability to mask malicious activity as standard system maintenance or updates.
When the user executes the downloaded BAT file, it displays a fake “Windows Media Player Component Update” screen in the command console.
This visual ruse conditions the victim to expect and accept subsequent security prompts, believing they are simply authorizing a legitimate software update required for audio playback functionality.
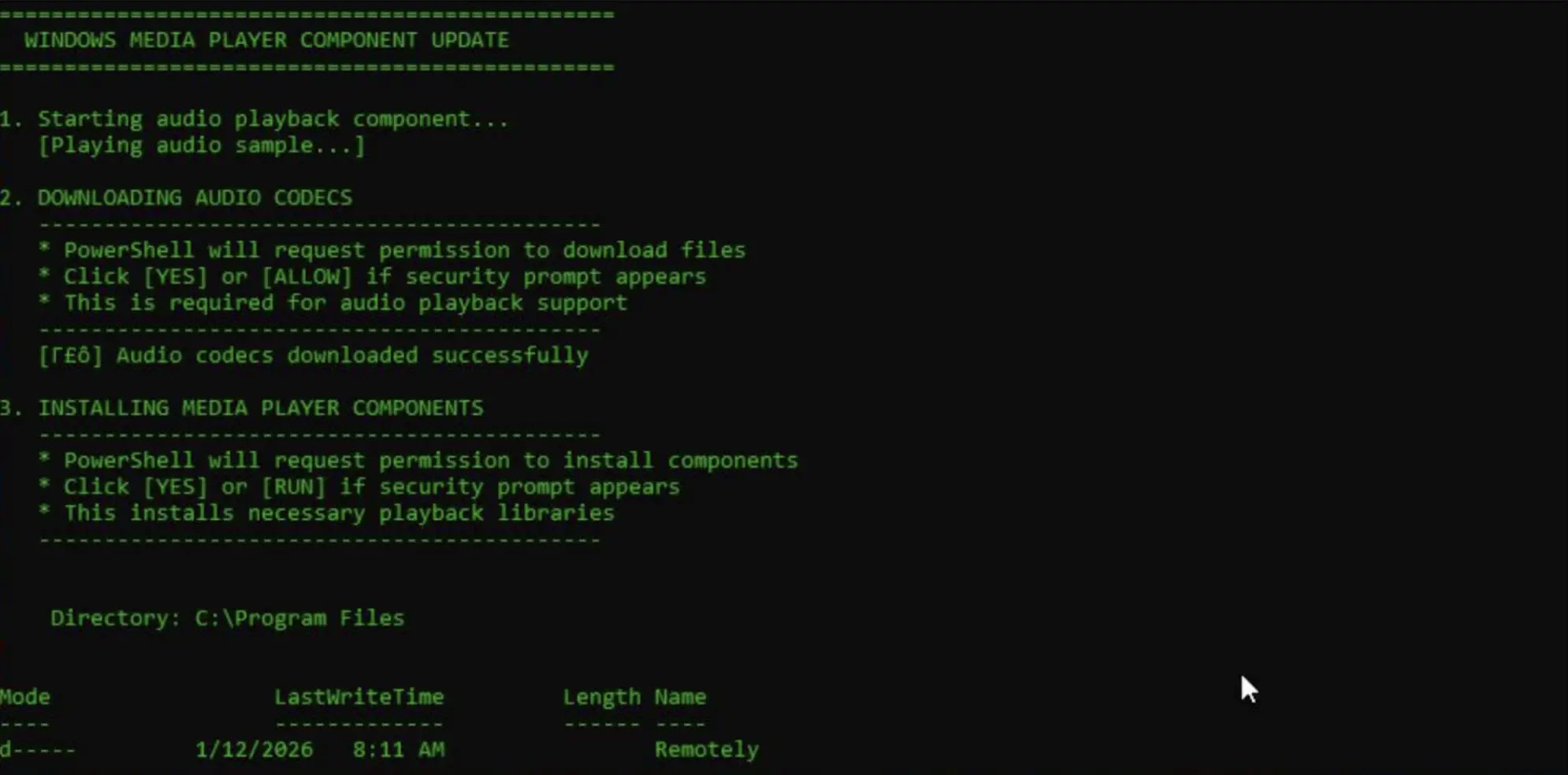
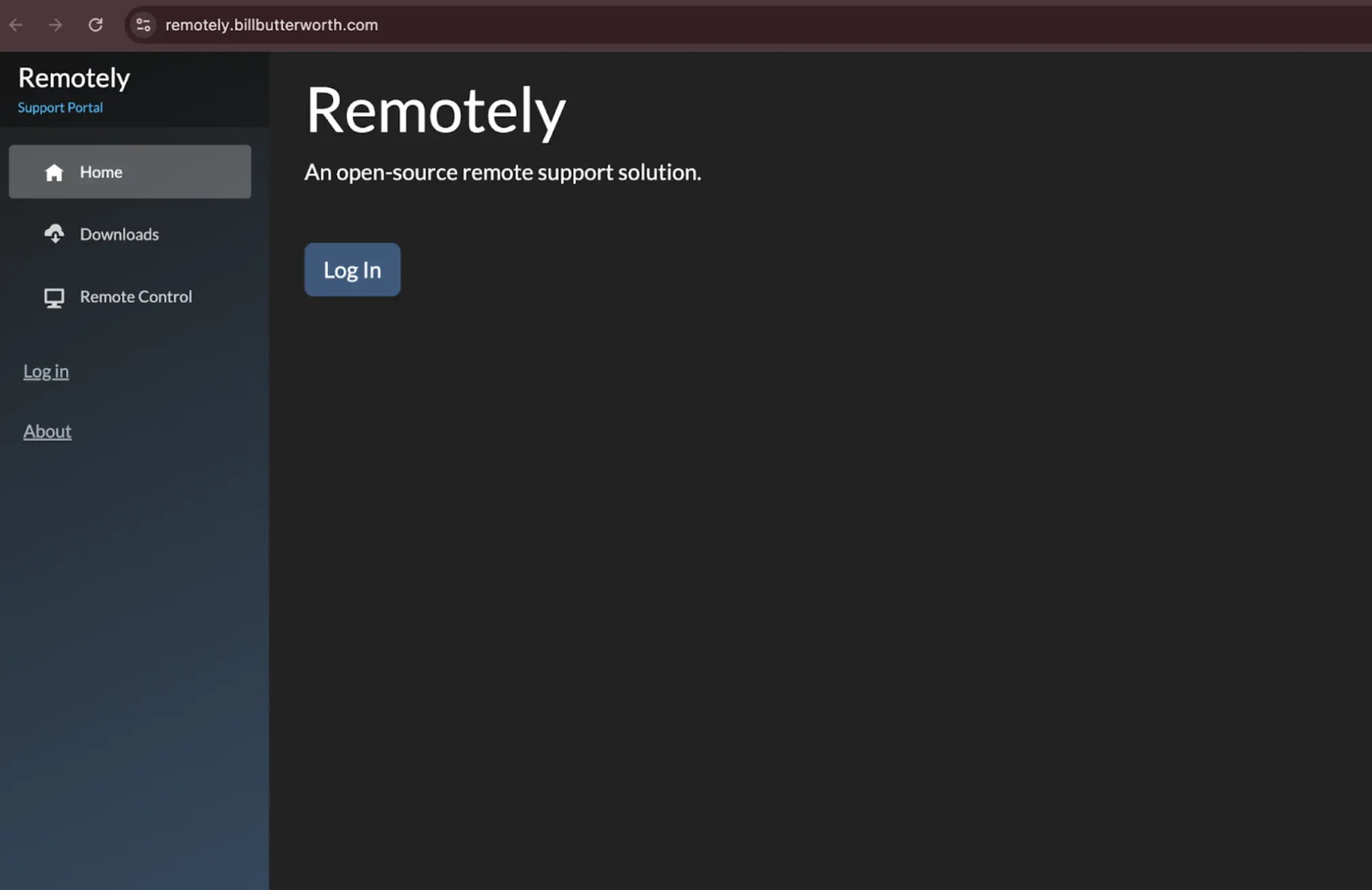
While the decoy update screen runs in the foreground, the script quietly downloads and installs “Remotely,” a legitimate open-source remote monitoring and management (RMM) tool.
To further maintain the illusion, the malware simultaneously plays a benign audio file from a minimized browser window, providing sensory confirmation to the victim that the “voicemail” works.
Meanwhile, the installed RMM agent enrolls the device into an attacker-controlled network, granting them persistent remote access to the system to steal data or deploy further payloads.
To protect against these threats, security teams should actively monitor for unauthorized RMM software installations and block known malicious domains associated with this campaign.
Users are advised to inspect URLs carefully before clicking and to treat any request to download “codecs” or “updates” merely to play a voicemail message with extreme suspicion.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.