Microsoft Disables NTLM by Default for Secure Authentication
Microsoft is accelerating the deprecation of NTLM (New Technology LAN Manager). This legacy authentication protocol has been a foundational component of Windows for over three decades. The company...
Microsoft is accelerating the deprecation of NTLM (New Technology LAN Manager). This legacy authentication protocol has been a foundational component of Windows for over three decades.
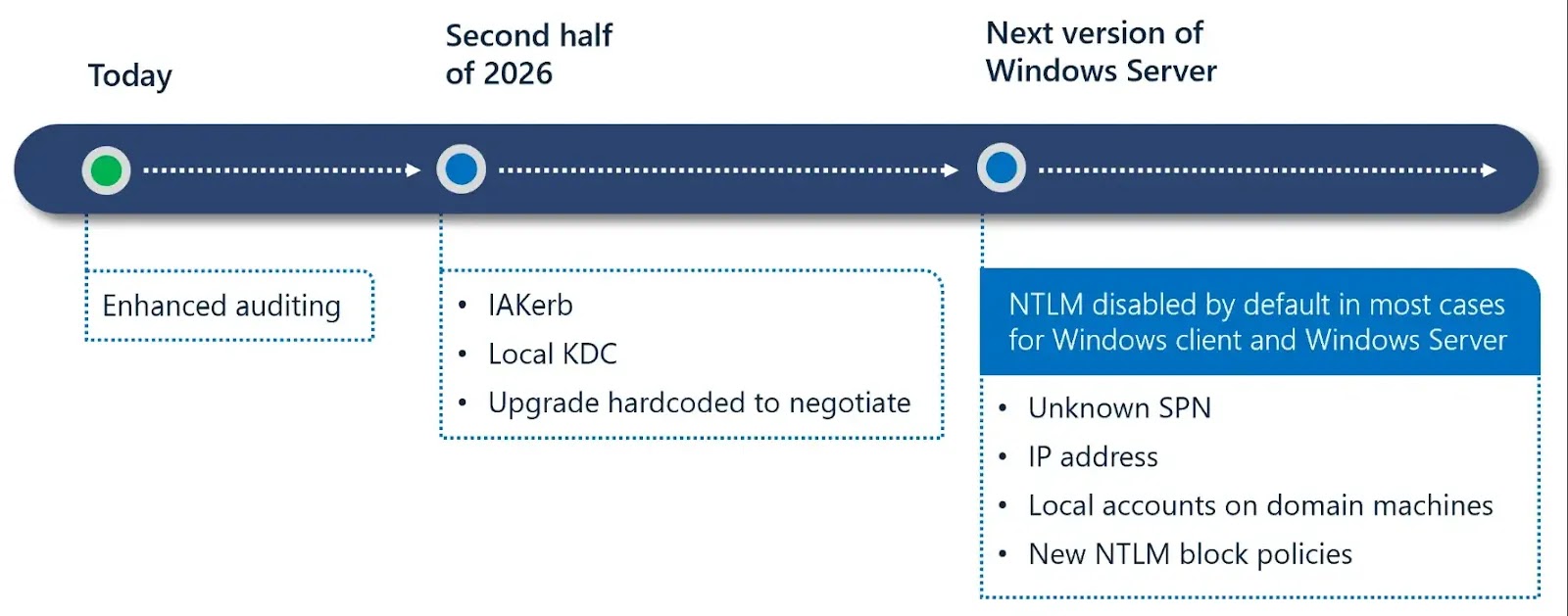
The company has announced a phased roadmap to reduce, restrict, and ultimately disable NTLM by default in upcoming Windows releases, marking a significant evolution in Windows authentication security.
NTLM has long served as a fallback authentication mechanism when Kerberos is unavailable.
However, the protocol’s age and inherent cryptographic weaknesses make it vulnerable to replay, relay, and pass-the-hash attacks.
Three-Phase Roadmap for Smooth Transition
As modern security threats continue to evolve, NTLM’s susceptibility to these attack vectors poses significant risks to enterprise environments.
Microsoft’s decision to disable NTLM by default reflects the need to adopt stronger, Kerberos-based authentication mechanisms that align with contemporary security standards.
The transition follows a three-phase approach designed to minimize organizational disruption.
| Phase | Timeline | Key Focus | Details |
|---|---|---|---|
| Phase 1 | Available now | Visibility & Auditing | Shows where NTLM is used across systems. |
| Phase 2 | Second half of 2026 | Reduce NTLM Usage | Enables Kerberos in NTLM fallback cases. |
| Phase 3 | Future Windows release | Disable by Default | NTLM off by default with legacy support. |
Importantly, Microsoft will provide built-in support for handling legacy NTLM-only scenarios. Minimizing application breakage for organizations with older systems or custom applications.
Backward Compatibility Maintained During Migration
The company emphasizes that disabling NTLM by default does not mean complete removal.
NTLM will remain present in the operating system and can be re-enabled via policy if necessary, ensuring backward compatibility during the transition period.
This approach balances meaningful security improvements with practical organizational needs.
Organizations should begin preparing now by deploying enhanced NTLM auditing, mapping application dependencies, and migrating workloads to Kerberos.
Testing NTLM-disabled configurations in non-production environments. Microsoft encourages enterprises to engage identity, security, and application owners to ensure smooth transitions.
For organizations facing unique NTLM-dependent scenarios, Microsoft has established ntlm@microsoft[.]com as a point of contact.
This phased, collaborative approach positions Windows for a more secure, passwordless future while maintaining supported migration pathways for enterprise environments.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.