Punishing Owl Hacker Group Targets Russian Security Agency
A previously unknown hacktivist group, Punishing Owl, has launched sophisticated cyberattacks targeting Russian government security agencies. The group first surfaced on December 12, 2025, when it...
A previously unknown hacktivist group, Punishing Owl, has launched sophisticated cyberattacks targeting Russian government security agencies.
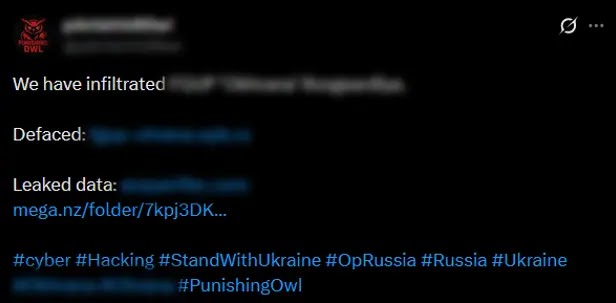
The group first surfaced on December 12, 2025, when it announced the successful breach of a Russian government security agency’s network.
The attackers published stolen internal documents on a data leak site and duplicated the files on a Mega.nz repository, demonstrating their intention to maximize public exposure of the compromise.
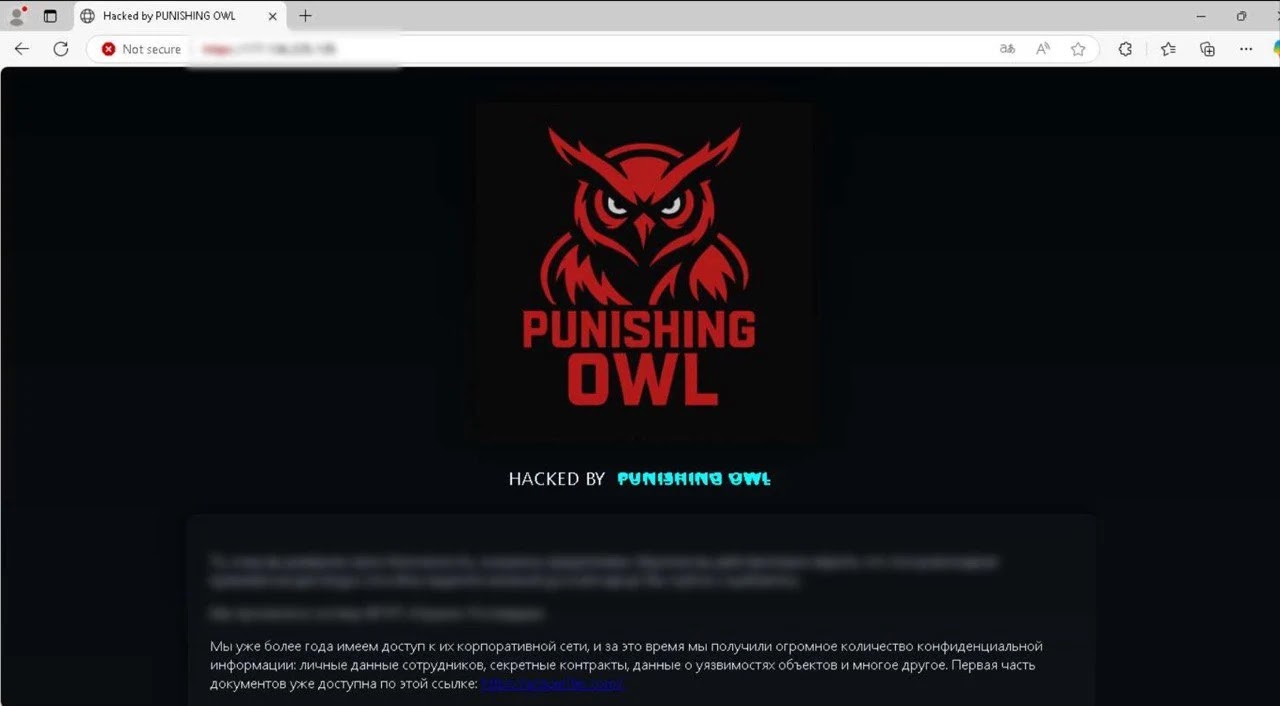
The group employed multiple attack methods to amplify the impact of their operation. After gaining access to the victim’s DNS configuration, Punishing Owl created a subdomain and modified DNS records to redirect traffic to a server located in Brazil.
This server hosted the stolen files along with a political manifesto explaining their motives.
The attackers strategically chose Friday evening at 6:37 PM to announce the breach, timing calculated to delay response efforts and ensure maximum visibility of their activities.
Following the initial breach, the group launched business email compromise attacks against the victim’s partners and contractors.
Habr analysts identified that Punishing Owl sent emails from a Brazilian server using addresses created within the victim’s email domain.
These messages falsely claimed to confirm the network compromise and included urgent requests to review attached documents.
The attack infrastructure revealed technical sophistication despite the group’s recent emergence.
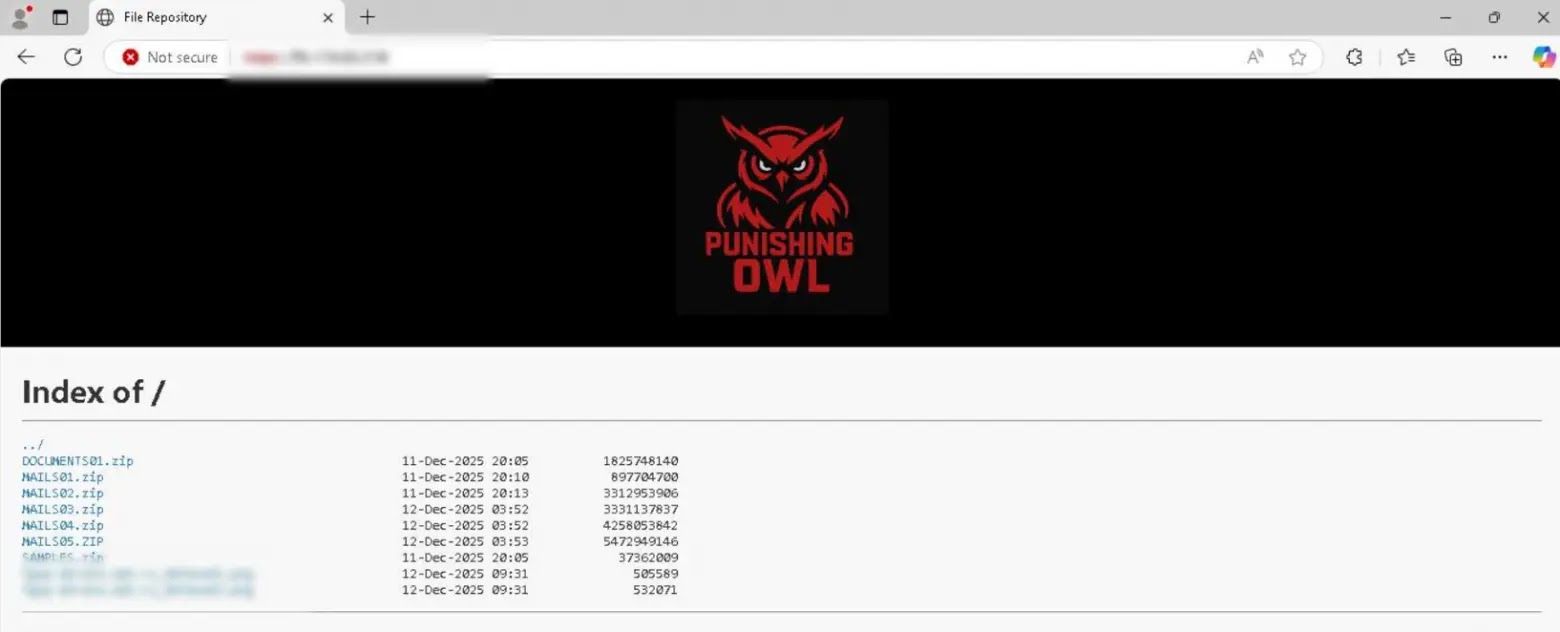
Punishing Owl configured fake TLS certificates, established IMAP and SMTP services for email operations, and deployed the ZipWhisper PowerShell stealer to harvest browser credentials from infected systems.
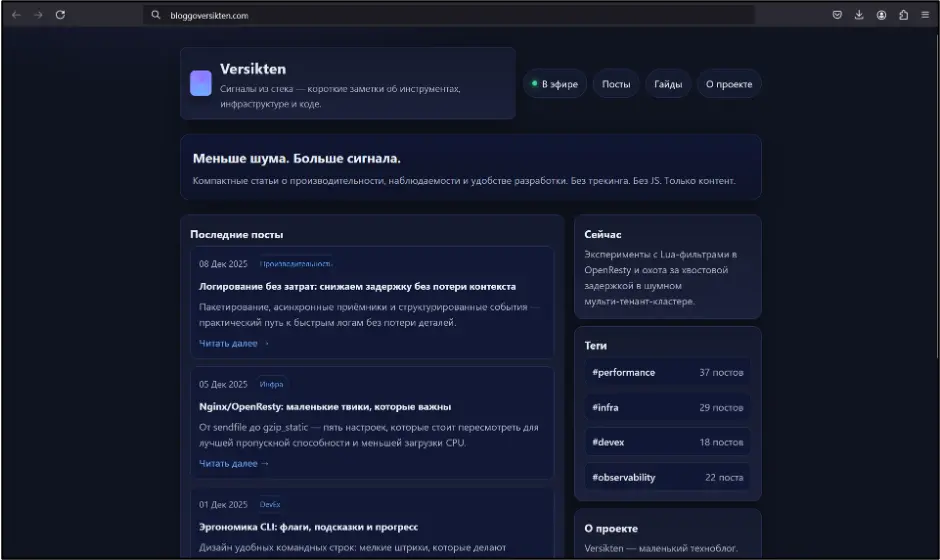
The malicious emails contained password-protected ZIP archives with disguised LNK files that executed PowerShell commands, downloading the stealer from a command-and-control server at bloggoversikten[.]com.
Infection Mechanism and Credential Theft
The ZipWhisper stealer operates through a multi-stage infection process designed to extract sensitive browser data from compromised hosts.
When victims open the disguised LNK file, it silently executes PowerShell commands that download the stealer payload from the attacker’s infrastructure.
The malware then collects files containing web browser credentials, cookies, and saved passwords, packaging them into ZIP archives with specific naming patterns that include the username and chunk numbers.
These archives are stored temporarily in the AppData/Local/Temp directory before being uploaded to the command-and-control server through a customized endpoint structure.
Analysis of the stealer’s code revealed comments suggesting the possible use of AI tools to generate portions of the malicious script, indicating the group may be leveraging modern development techniques to accelerate their operations against Russian critical infrastructure targets.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.








No Comment! Be the first one.