GhostChat Spyware Steals Sensitive Android Data via WhatsApp
A new Android spyware campaign has emerged, directly targeting users in Pakistan. This sophisticated operation leverages romance scams and fake dating profiles to illicitly acquire personal...
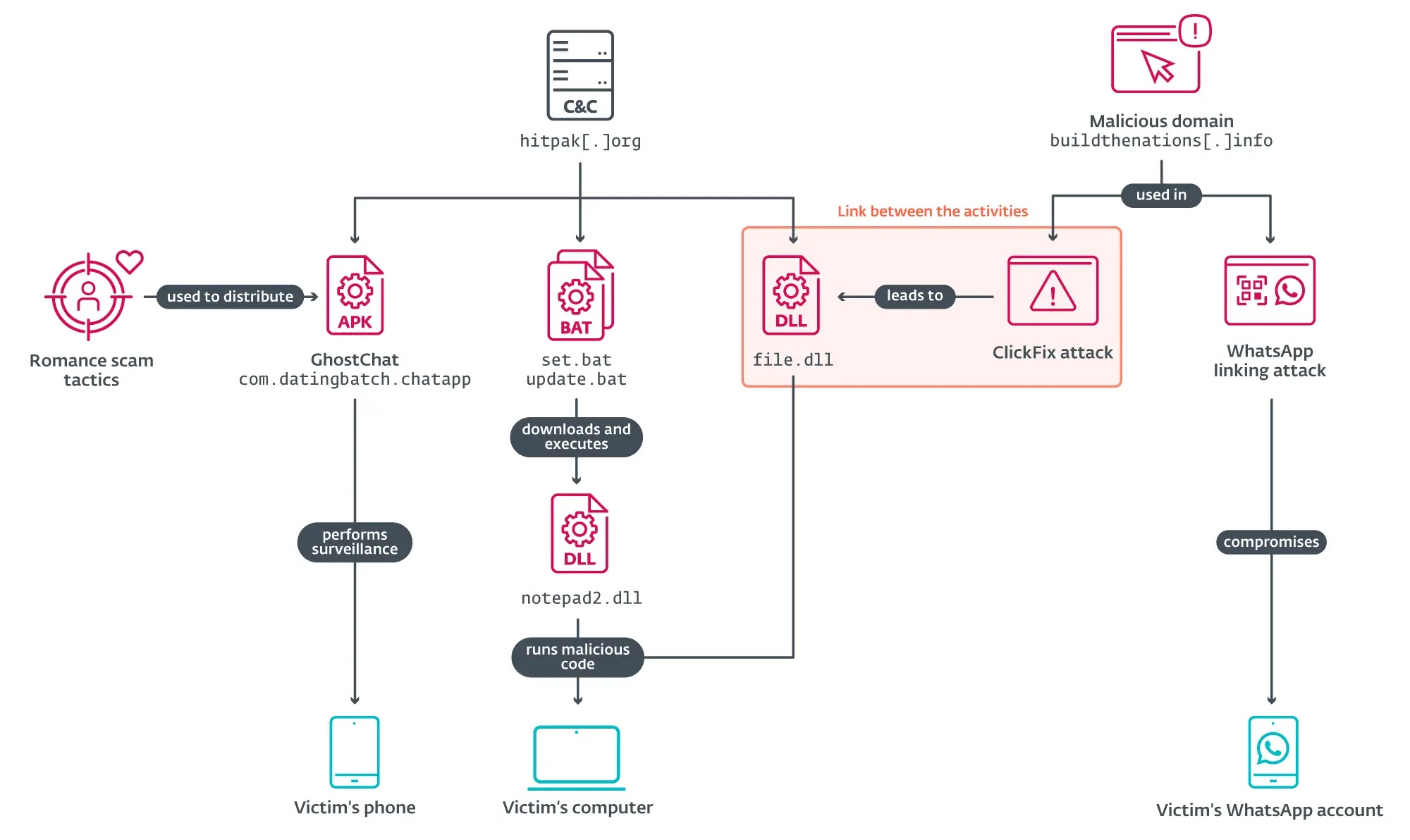
A new Android spyware campaign has emerged, directly targeting users in Pakistan. This sophisticated operation leverages romance scams and fake dating profiles to illicitly acquire personal information.
The malicious application, known as GhostChat, disguises itself as a legitimate chat platform while secretly running surveillance operations in the background.
This attack represents a dangerous trend where cybercriminals combine social engineering tactics with advanced spyware capabilities to compromise mobile devices and access sensitive data.
The spyware campaign was discovered after a suspicious Android application was uploaded to VirusTotal from Pakistan in September 2025. GhostChat masquerades as a dating app called “Dating Apps without payment,” using the icon of a legitimate application available on Google Play.
However, the malicious version has never been distributed through official app stores, requiring victims to manually install it by enabling permissions for apps from unknown sources.
This distribution method helps the threat actors avoid detection by Google Play Protect during the initial installation phase.
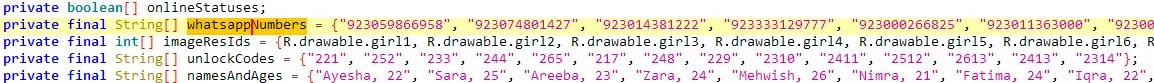
Welivesecurity analysts noted that GhostChat employs an unusual layer of deception that sets it apart from typical mobile threats. The app presents 14 fake female profiles, each marked as “Locked” and requiring passcodes to access.
These codes are hardcoded within the application and distributed alongside the app to create an illusion of exclusive access for potential victims.
Once a victim enters the correct unlock code, they are redirected to WhatsApp to initiate conversations with numbers operated by the threat actors, all bearing Pakistani country codes to enhance the scam’s credibility.
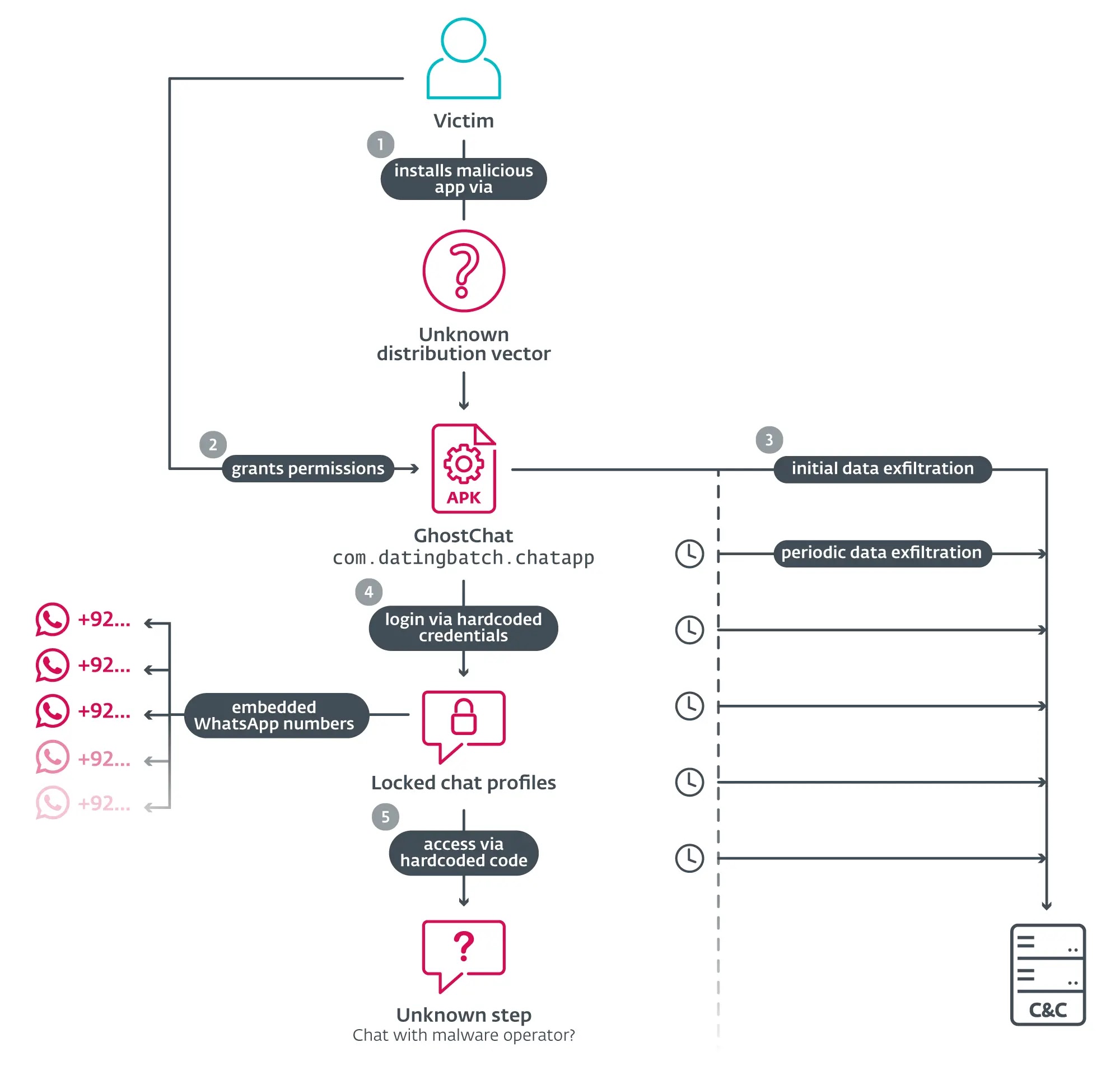
While victims engage with what they believe are real dating profiles, the spyware operates silently in the background, exfiltrating device data to a command-and-control server.
The malware immediately collects device identifiers, contact lists, and files stored on the device including images, PDFs, and Microsoft Office documents.
GhostChat establishes continuous surveillance by setting up content observers that monitor newly created images and scheduling periodic scans every five minutes to detect new documents, ensuring ongoing data harvesting throughout the infection period.
Infection Mechanism and Persistence Tactics
GhostChat demonstrates sophisticated infection and persistence mechanisms designed to maintain long-term access to compromised devices.
Upon installation, the application requests multiple permissions that appear standard for a chat application but actually enable extensive surveillance capabilities.
The spyware leverages Android’s BOOT_COMPLETED broadcast intent, allowing it to automatically activate whenever the device restarts, ensuring persistent operation even after reboots.
The malware employs foreground persistence techniques to keep its surveillance service continuously running without user awareness.
This method prevents Android’s battery optimization features from terminating the spyware process, maintaining uninterrupted access to device resources.
The application communicates with its command-and-control infrastructure using HTTPS requests, making detection more difficult as the traffic appears similar to legitimate encrypted communications.
GhostChat’s architecture supports both immediate data exfiltration upon first execution and sustained monitoring throughout the infection lifecycle, creating a comprehensive surveillance framework that operates independently of user interaction with the fake dating interface.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.