Google Disrupts World’s Largest IPIDEA Residential Proxy Network
This week, Google and its partners initiated a significant operation aimed at dismantling IPIDEA, a residential proxy network widely regarded by security experts as one of the world’s largest....
This week, Google and its partners initiated a significant operation aimed at dismantling IPIDEA, a residential proxy network widely regarded by security experts as one of the world’s largest.
The proxy service operates by routing internet traffic through millions of everyday consumer devices scattered across the globe, allowing attackers to hide their activities behind ordinary IP addresses.
This infrastructure has become a critical tool for criminals and nation-state groups seeking to mask their digital footprints while conducting cyberattacks, espionage campaigns, and data theft operations.
The IPIDEA network represents a significant threat because it sells access to a massive pool of compromised residential IP addresses—devices from the United States, Canada, and Europe being particularly valuable.
Attackers use these addresses to make their malicious actions appear to come from normal internet users rather than themselves, making detection and blocking far more difficult for network defenders and security teams.
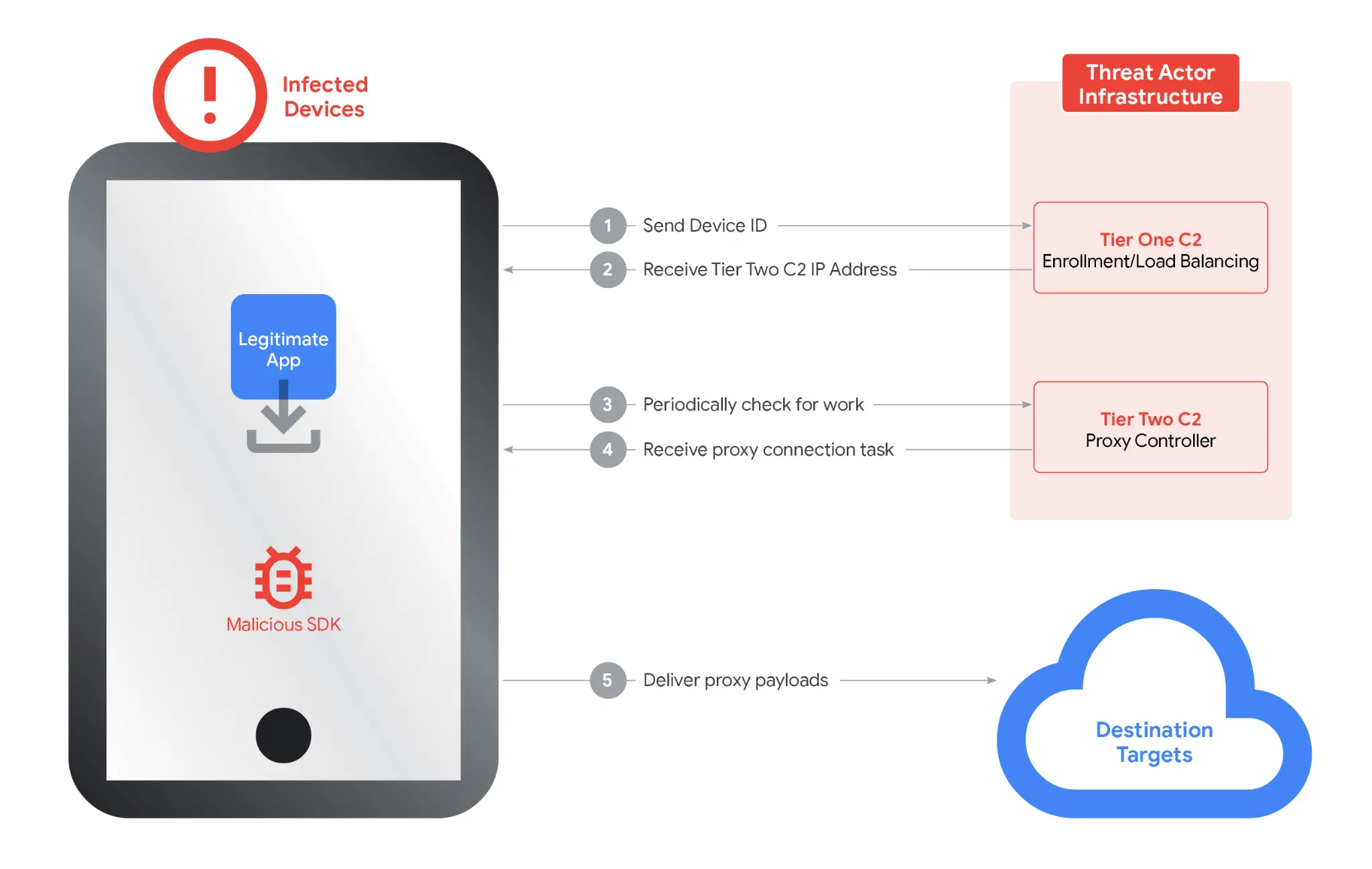
Google Cloud analysts and researchers noted that IPIDEA operates through software development kits, known as SDKs, which developers unknowingly embed into legitimate-looking applications.
When users download games, utilities, or other apps containing these hidden SDKs, their devices become part of the proxy network without their knowledge or clear consent.
The company uses multiple brand names—including 360 Proxy, Luna Proxy, and others—to disguise the fact that all these services are controlled by the same group of operators.
Infection mechanism
The infection mechanism relies on deception rather than complex malware exploits. IPIDEA SDKs remain dormant inside regular applications until activated, silently converting user devices into proxy exit nodes.
Once embedded, these SDKs establish two-tier command-and-control communication systems: first connecting to control servers to receive instructions, then maintaining persistent connections to proxy distribution servers.
This architecture allows attackers to route their malicious traffic through infected devices automatically.
Google’s investigation revealed that during just one seven-day period in January 2026, over 550 tracked threat groups used IPIDEA exit nodes for various attacks, including access to business systems and password spray operations targeting corporate infrastructure.
Google’s enforcement actions targeted the control infrastructure, legal domains used for marketing, and worked with platform partners including Cloudflare.
The company integrated protections into Google Play services, ensuring that Android devices automatically detect and remove applications containing IPIDEA code.
These coordinated efforts have significantly reduced the network’s operational capacity by eliminating millions of available device nodes, though security experts warn that similar proxy networks continue expanding globally.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.