Attackers Exploit Canadian Digital Service Reliance
Cyberattackers are increasingly exploiting Canadian citizens’ significant reliance on online government and commercial services. From paying traffic fines and renewing licenses to tracking...
Cyberattackers are increasingly exploiting Canadian citizens’ significant reliance on online government and commercial services.
From paying traffic fines and renewing licenses to tracking parcels and booking flights, people now expect these tasks to be quick and digital.
Threat actors are taking advantage of this trust by building fake portals that look almost identical to official Canadian websites, tricking victims into sharing sensitive data and payment details.
These attacks do not rely on complex malware running silently on a device. Instead, they weaponize urgency, fear, and brand trust.
SMS messages and online ads warn users about unpaid tickets, failed deliveries, or booking problems and push them toward lookalike domains.
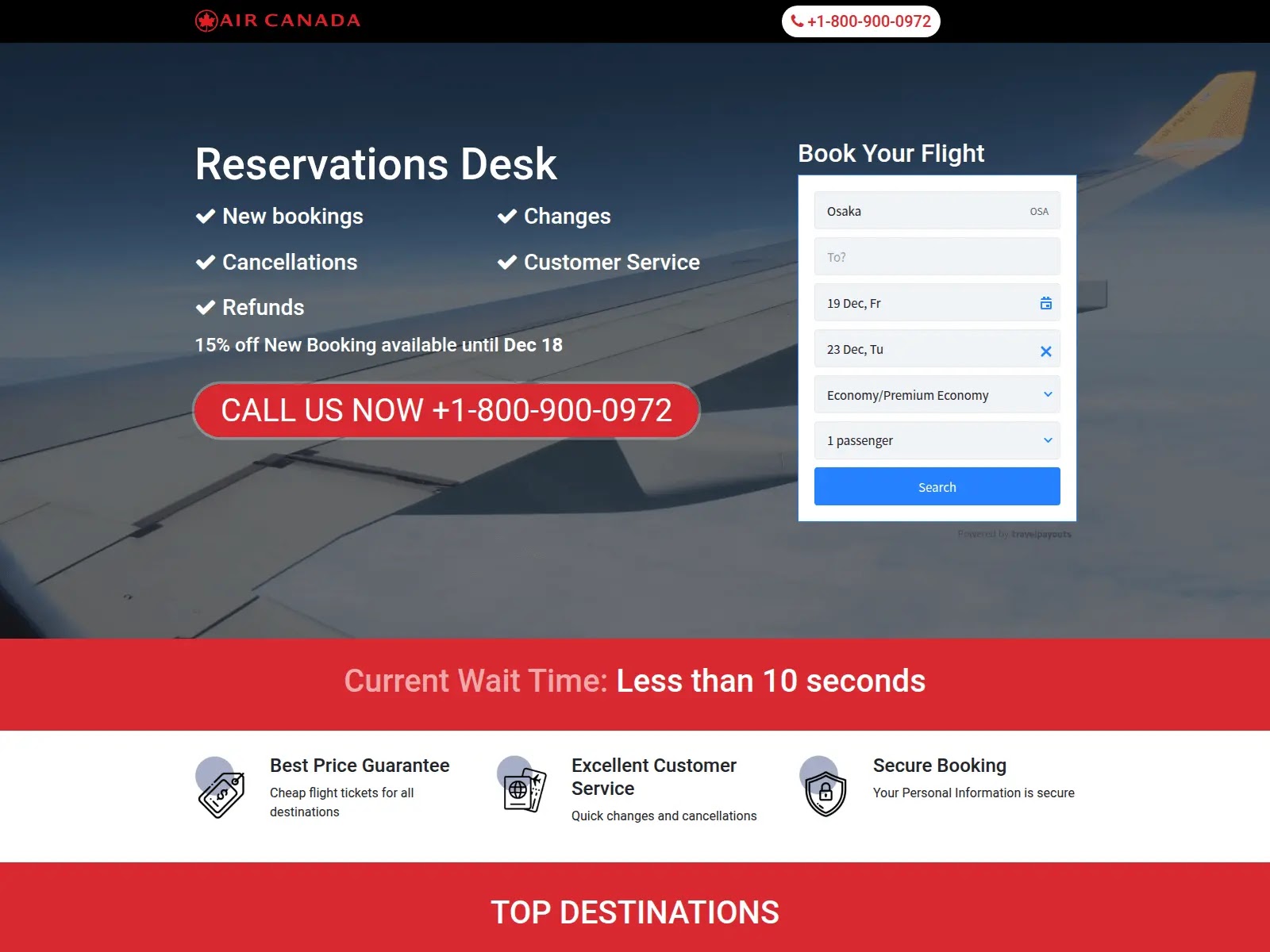
CloudSEK analysts identified multiple fraud clusters that impersonate PayBC, ServiceOntario, Canada Post, the Canada Revenue Agency (CRA), and Air Canada, all designed to harvest personal and financial information at scale.
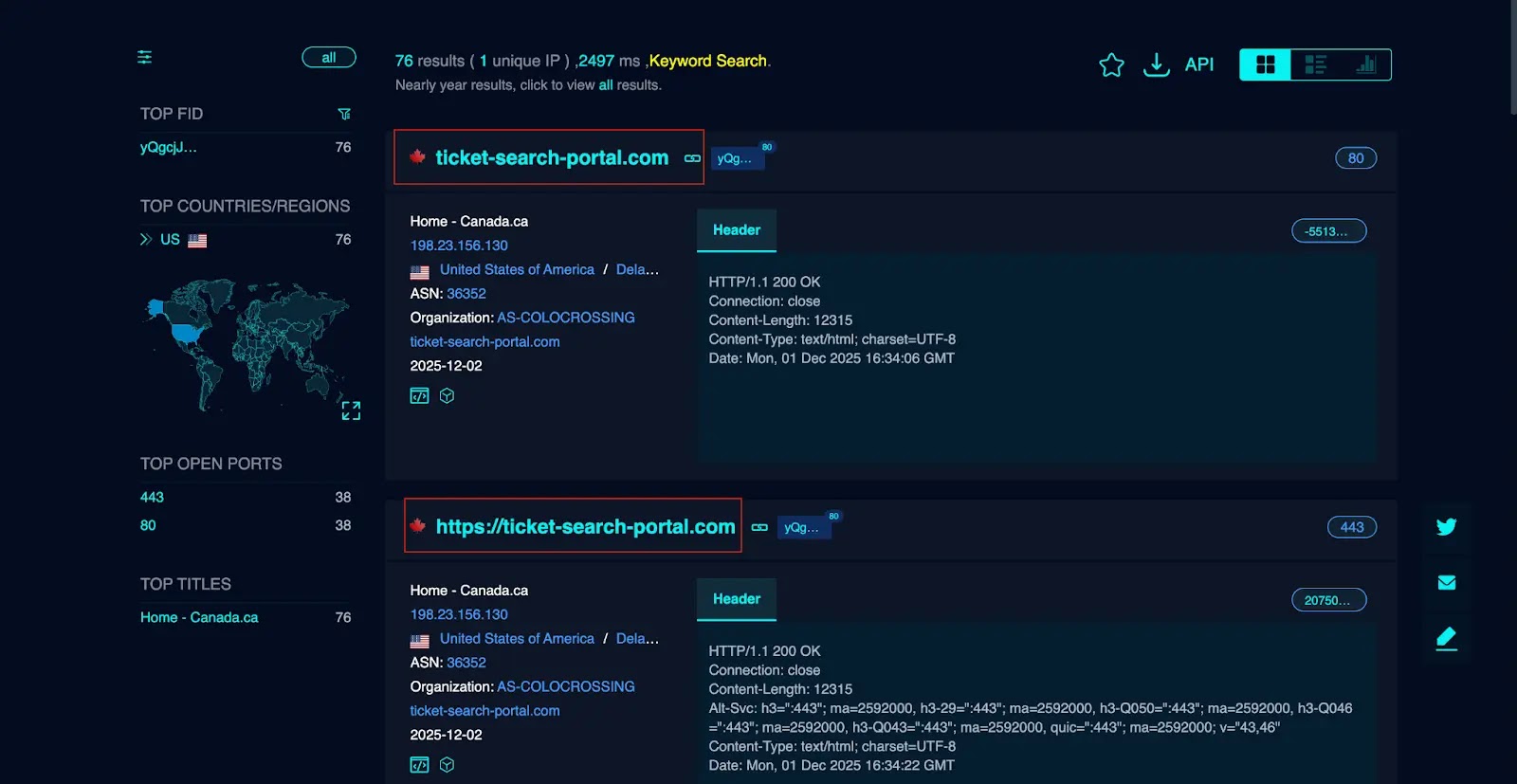
CloudSEK researchers noted that a major part of this activity is tied to the “PayTool” phishing ecosystem, a fraud framework focused on traffic fines and violation payments.
Shared infrastructure and phishing kits
Its operators use shared infrastructure and phishing kits that can be quickly reused and rebranded for new lures, allowing them to expand from provincial portals into what appears to be a central Government of Canada entry point.
At the heart of this ecosystem is an advanced impersonation infrastructure that simulates a unified traffic ticket search service.
Victims land on portals branded with the Government of Canada logo and provincial seals, where they are invited to select their province and search for supposed violations.
This design mirrors how legitimate federal websites route users to provincial services, deepening the sense of authenticity.
Once users start interacting with these portals, the infection mechanism unfolds through a staged flow. First, a fake validation step asks for ticket numbers, license details, or booking IDs, but accepts any input.
This step is not about verification; it is about building trust and keeping the victim engaged. After this, the site redirects to a counterfeit payment gateway that copies the layout of real processors.
Here, the attackers capture names, addresses, card data, and banking credentials, which can later be used for direct fraud or sold on underground markets.
Because the entire chain runs in the browser, these campaigns can evade many traditional endpoint controls.
The real defense lies in user awareness, strict domain checks, and stronger monitoring for suspicious Canada-themed portals before they reach Canadian citizens.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.