Spear Phishing Attack Uses Argentine Court Rulings
Argentina’s judicial sector is currently under attack from a sophisticated spear-phishing campaign. This operation leverages trust in legitimate court communications to deploy a dangerous...
Argentina’s judicial sector is currently under attack from a sophisticated spear-phishing campaign. This operation leverages trust in legitimate court communications to deploy a dangerous Remote Access Trojan.
The campaign uses authentic-looking federal court documents about preventive detention reviews to trick legal professionals into downloading malware.
Security experts have classified this attack as highly targeted, employing multi-stage infection techniques to gain long-term access to sensitive legal and institutional systems.
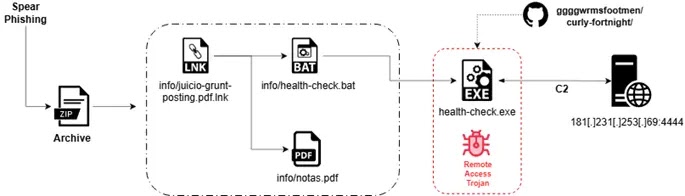
The attack begins when recipients receive emails containing a ZIP archive that appears to be an official judicial notice.
Inside the archive, attackers have planted a weaponized Windows shortcut file disguised as a PDF, along with a batch script loader and a legitimate-looking court resolution document.
Once the victim clicks on what appears to be a standard PDF file, the malicious execution chain activates while simultaneously displaying a convincing decoy document to avoid suspicion.
This social engineering technique makes the attack particularly effective against judicial personnel who routinely handle court-related documents.
Seqrite analysts identified this campaign and uncovered its sophisticated multi-stage delivery mechanism.
The research team discovered that the malware specifically targets Argentina’s legal sector, including judicial institutions, legal professionals, and government bodies connected to the justice system.
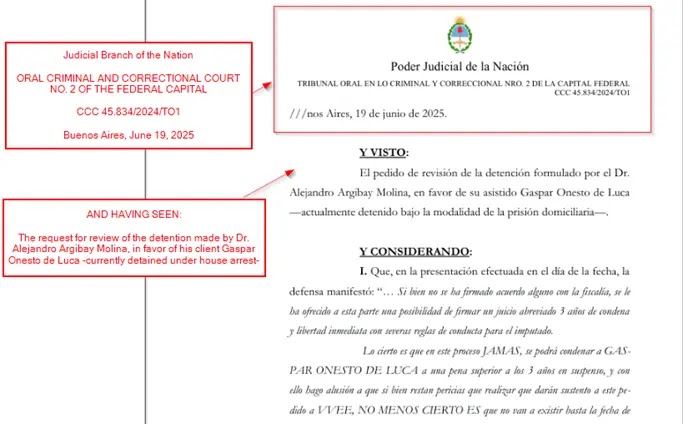
The decoy document mimics authentic Argentine federal court resolutions with remarkable precision, featuring formal legal Spanish, proper case numbering, judicial signatures, and references to real institutions like the Tribunal Oral en lo Criminal y Correccional.
This level of detail significantly increases the campaign’s success rate among its intended victims.
Infection Mechanism: From Shortcut to RAT Deployment
The attack uses a three-stage infection process designed to evade detection. The weaponized LNK file launches PowerShell in hidden mode, bypassing execution policies to run a batch script that connects to GitHub-hosted infrastructure.
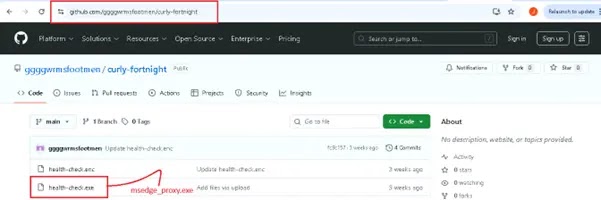
This script downloads a second-stage payload disguised as “msedge_proxy.exe,” stored in the Microsoft Edge user data directory to appear legitimate.
The final payload is a Rust-based Remote Access Trojan equipped with extensive anti-analysis capabilities.
The RAT performs comprehensive environment checks before execution, scanning for virtual machines, sandboxes, and debugging tools. If analysis tools are detected, the malware immediately terminates to avoid investigation.
Once operational, it establishes encrypted command-and-control communication, offering attackers capabilities including file exfiltration, persistence installation, credential harvesting, and even ransomware deployment through modular DLL components.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.