Hackers Use Hugging Face & ClawHub to Deploy Malware
An active malware distribution campaign is leveraging prominent AI platforms Hugging Face and ClawHub to deploy trojans, cryptominers, and infostealers. These malicious payloads masquerade as...
An active malware distribution campaign is leveraging prominent AI platforms Hugging Face and ClawHub to deploy trojans, cryptominers, and infostealers. These malicious payloads masquerade as legitimate AI tools and agent extensions.
The campaign marks a significant evolution in supply chain attacks, shifting from traditional software repositories to trusted AI ecosystems.
Within the OpenClaw ecosystem distributed through ClawHub, Acronis TRU identified 575 malicious skills published across 13 developer accounts.
The campaign appears to be primarily driven by two threat actors: “hightower6eu,” responsible for 334 malicious skills (58%), and “sakaen736jih,” responsible for 199 skills (34.6%), with the remaining 11 accounts contributing smaller volumes.
These trojanized skills masquerade as useful tools such as a YouTube transcript summarizer while secretly instructing users to download password-protected archives or execute encoded commands.
Hugging Face and ClawHub Leveraged
For Windows targets, payloads were detected as trojans packed with VMProtect. For macOS, a base64-encoded command connects to an external IP (91.92.242[.]30) and silently downloads and executes AMOS Stealer, a macOS-focused infostealer commonly sold as malware-as-a-service (MaaS) through Telegram and underground forums.
A second Windows payload used a 30-byte XOR key to decrypt strings at runtime, dynamically resolved NT APIs, and performed in-memory process injection into explorer.exe.
The injected code established AES-encrypted C2 communication over HTTPS to hxxps://velvet-parrot[.]com:443, downloaded a cryptominer disguised as svchost.exe, and maintained persistence via scheduled tasks and Windows Defender exclusion paths.
A critical technique observed across ClawHub campaigns is indirect prompt injection, which embeds hidden, malicious instructions within skill files that AI agents read and execute on behalf of users.
Because OpenClaw agents are designed to act autonomously based on instructions in skill definitions, attackers can effectively turn these agents into unwitting intermediaries, expanding attack impact far beyond the initial victim.
On Hugging Face, which hosts over one million machine learning models, Acronis TRU identified repositories serving as multi-stage infection chain staging points, hosting payloads across Windows, Linux, and Android. Two tracked campaigns illustrate this abuse in practice.
The ITHKRPAW campaign, targeting Vietnamese financial sector organizations in January, used a malicious LNK file to invoke Cloudflare Workers, which served a PowerShell dropper that fetched a payload from a Hugging Face dataset repository while opening a decoy cat image to mask activity.
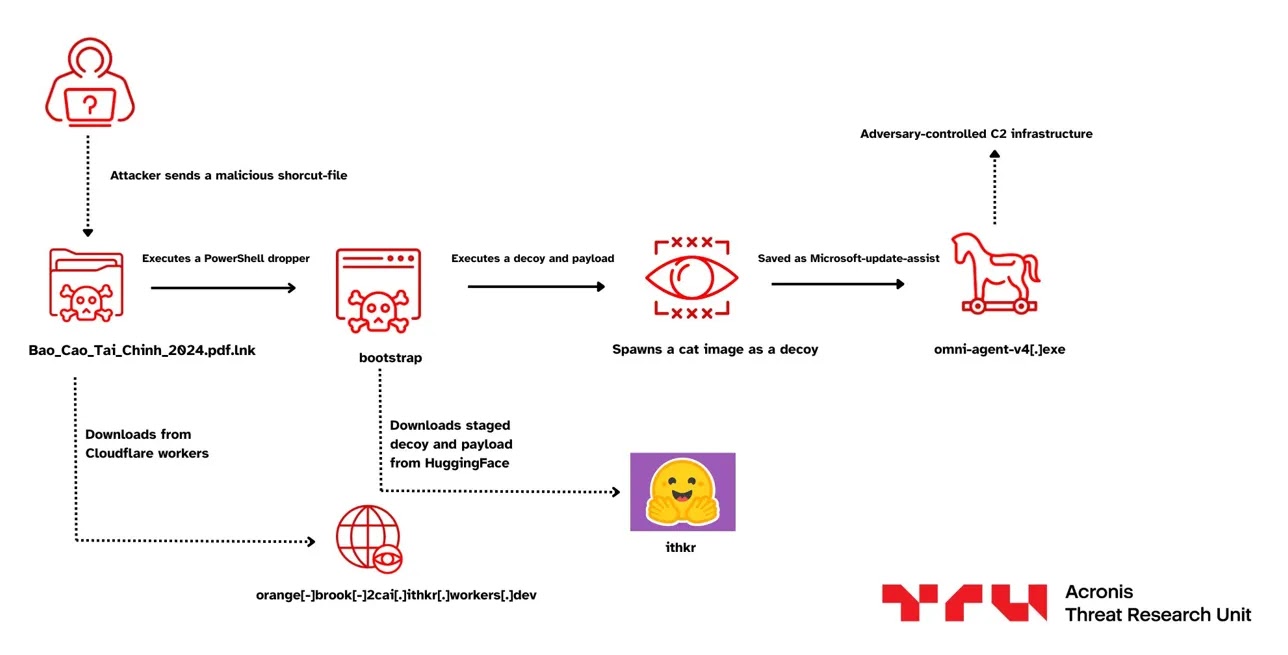
Researchers assess with moderate confidence that the PowerShell script was LLM-generated, based on embedded Vietnamese-language comments.
The FAKESECURITY campaign used a batch script (CDC1.bat) containing an encoded PowerShell blob that downloaded a heavily obfuscated secondary batch script from a Hugging Face repository.
After stripping the Mark-of-the-Web to bypass Windows SmartScreen, the malware injected shellcode into explorer.exe and dropped a file masquerading as Windows Security.
Organizations and developers should treat AI models, datasets, and agent extensions as untrusted inputs requiring the same validation applied to any third-party code.
Specific steps include auditing installed OpenClaw skills for encoded commands or external download instructions, monitoring for unexpected process injection into explorer.exe, blocking known malicious indicators (91.92.242[.]30, velvet-parrot[.]com), and restricting Windows Defender exclusion path modifications via Group Policy.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.







No Comment! Be the first one.