NWHStealer Uses Bun Loader, Anti-VM Delivery Chain
Cybersecurity researchers are closely monitoring an evolving threat: NWHStealer, a Windows-based information stealer. The malware has resurfaced with a significantly more sophisticated delivery...
Cybersecurity researchers are closely monitoring an evolving threat: NWHStealer, a Windows-based information stealer. The malware has resurfaced with a significantly more sophisticated delivery chain, now leveraging the Bun JavaScript runtime as a key component of its infection process. A
NWHStealer is a Rust-based malware capable of stealing sensitive data from infected Windows systems. It spreads through Node.js scripts, MSI installers, and fake software downloads hosted on trusted platforms such as GitHub, GitLab, SourceForge, and Itch.io. Since it blends into legitimate-looking software packages, many users unknowingly download and run it without any suspicion.
Analysts at Malwarebytes identified the new delivery method during routine threat hunting activities.
Researcher Gabriele Orini noted that attackers have now incorporated Bun, a modern JavaScript toolkit built as a high-performance alternative to Node.js, into the malware’s delivery chain. Its relative newness in security circles makes it particularly appealing to attackers trying to slip past detection.
Once inside a system, NWHStealer is highly capable. It collects system information, steals saved browser data and passwords, drains cryptocurrency wallets, and targets applications like Discord, Steam, and FTP clients such as FileZilla.
It can also inject malicious code into browser processes, bypass Windows User Account Control, persist through scheduled tasks, and pull new command-and-control addresses from Telegram to keep the operation alive after partial takedowns.
The scale of this campaign is notable. Attackers continue to create fresh profiles on legitimate platforms to push new lures, making it difficult for moderators to respond quickly. The combination of data theft, persistence, and self-updating infrastructure makes NWHStealer a serious threat to both everyday users and organizations.
Bun Loader, Anti-VM Checks, and Encrypted C2
The infection begins with a ZIP archive disguised as a game trainer, software crack, or utility tool. Detected archive names include MOUSE_PI_Trainer_v1.0.zip, FiveM Mod.zip, TradingView-Activation-Script-0.9.zip, and AutoTune 2026.zip.
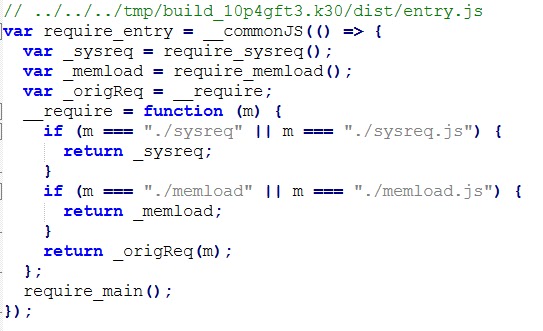
Inside sits Installer.exe, which carries JavaScript code bundled with the Bun runtime hidden within its .bun section.
The malicious JavaScript is divided into two key files. The first, sysreq.js, runs PowerShell and WMI commands to check whether the system is a real machine or a virtual one. It inspects CPU count, disk space, screen resolution, hardware manufacturers, and even the username, using a scoring system to decide whether to proceed with infection or stop entirely. This anti-VM layer is designed to avoid detection in automated security analysis environments.
The second file, memload.js, handles communication with the attacker’s command-and-control server. Strings and configurations are encrypted using XOR combined with base64 encoding, making static analysis much harder. The loader sends a report containing the victim’s public IP, system details, and a screenshot to the C2, then fetches an AES-encrypted payload and deploys NWHStealer directly into memory with minimal traces on disk.
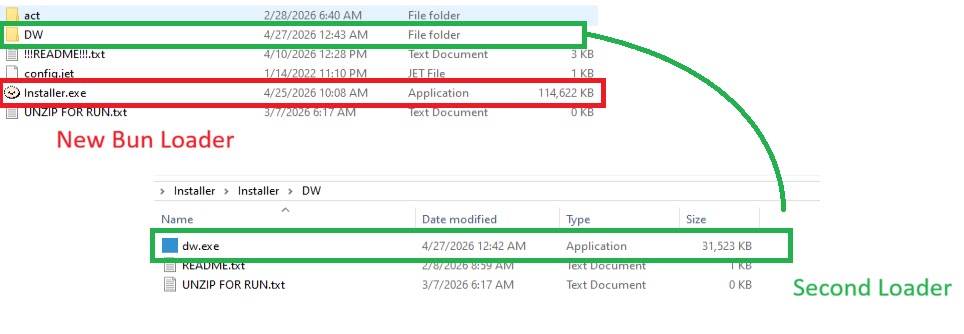
Some analyzed ZIP files also include a secondary loader called dw.exe inside a folder labeled “DW.” A Readme.txt inside the archive tells users to run dw.exe manually if the main installer fails, giving attackers a fallback option if the primary C2 server goes offline. This dual-loader setup reflects a deliberate backup plan to ensure delivery regardless of temporary disruptions.
Staying Safe From NWHStealer
Given how widely this stealer is distributed, users should take practical steps to protect themselves. Only download software from official, verified sources and avoid file-sharing platforms unless the publisher’s identity and reputation are clearly established.
Always check a file’s digital signature before running it, as legitimate software will carry consistent, verifiable signing details.
It is also worth inspecting any downloaded archive before opening it. Malicious archives often have unusual file structures, mismatched content, or naming patterns that do not match what was advertised.
Staying cautious with downloads that seem too good to be true, whether a game cheat, a software activator, or a free tool, remains one of the most effective defenses against threats like NWHStealer.
Indicators of Compromise (IoCs):-
| Type | Indicator | Description |
|---|---|---|
| Domain | whale-ether[.]pro | NWHStealer C2 server |
| Domain | cosmic-nebula[.]cc | NWHStealer C2 server |
| Domain | silent-harvester[.]cc | Bun Loader C2 server |
| Domain | silent-orbit[.]cc | Bun Loader C2 server |
| Domain | support-onion[.]club | Bun Loader C2 server |
| SHA-256 | d3a896f450561b2546b418b469a8e10949c7320212eb1c72b48e2b1e37c34ba5 | Malicious file hash |
| SHA-256 | 96fe4ddfe256dc9d2c6faea7c18e2583cd9d9c0099a4ad2cf082f569ee8379f4 | Malicious file hash |
| SHA-256 | 3710fb27d2032ef1eb1252ebf5c4dd516d2b2c0a83fb82c664c89e504b990fa9 | Malicious file hash |
| SHA-256 | 33d07aa24b217f27df6a483295c817da198e12511a6989bcc6b917feaf8e491d | Malicious file hash |
| SHA-256 | 5427b4cefb329ed0e9585b3ce58a2788baf87e3b0c7221373f9bbd5f32c85b62 | Malicious file hash |
| SHA-256 | 308da9f49ffa1d1744e428b567792ab22712159974e9da8d8e0414ecd81de93e | Malicious file hash |
| SHA-256 | 021838f30a43026084978bce187c165c6b640d8d474ec009d48078d21ec62025 | Malicious file hash |
| SHA-256 | c8e96b55f13435c4b43b7209d2403f1a0e0f9deb05edc50e0f777430be693b07 | Malicious file hash |
| SHA-256 | 0614c4cc6375ab6bdcdd2dfa913a67d32c3e8be9b95a4a2aa09bb131b98191c8 | Malicious file hash |
| SHA-256 | 0020999b2e3e4d1b2cfb69e4df9440d3ce05d508573889fdc12b724ce75a0cd8 | Malicious file hash |
| SHA-256 | 0fa42df08cc467ec52b2d388b5575114a8ec067d13f6b1a653ec33fe879f88ca | Malicious file hash |
| SHA-256 | 15f79980650393d182f81cd6e389210568aa1f5f875e515efe6cb9485d64b7fb | Malicious file hash |
| SHA-256 | 20454ba58d509300fd694ae6159db4efa1b7ff965f98c29e7d087e20f96578c1 | Malicious file hash |
Note: IP addresses and domains are intentionally defanged (e.g., [.]) to prevent accidental resolution or hyperlinking. Re-fang only within controlled threat intelligence platforms such as MISP, VirusTotal, or your SIEM.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.







No Comment! Be the first one.