Hackers Use Fake Claude AI Installers to Infect Systems
Cybercriminals are deploying deceptive websites impersonating Claude AI to lure users into installing malware. This campaign, identified as “InstallFix” or the Fake Claude Installer threat, marks a...
Cybercriminals are deploying deceptive websites impersonating Claude AI to lure users into installing malware. This campaign, identified as “InstallFix” or the Fake Claude Installer threat, marks a significant shift in how attackers exploit public trust in artificial intelligence tools.
Instead of targeting software vulnerabilities, these attackers are targeting human behavior, knowing that users will follow installation steps without question.
The method is simple and effective. Attackers set up fake Claude AI installation pages and use paid Google Ads to push those pages to the top of search results.
When someone searches for “Claude Code” or “Claude Code install,” a sponsored link appears first, looking exactly like a trusted result. One click leads to a fraudulent site that provides step-by-step instructions with commands tailored to the user’s operating system, either Windows or macOS.
Researchers at Trend Micro identified and documented the campaign, noting that the malware is not a simple infection. It is a multi-stage attack chain that collects system information, disables security features, creates scheduled tasks to survive reboots, and connects to attacker-controlled servers for further instructions.
Confirmed attacks span the United States, Malaysia, the Netherlands, and Thailand, hitting industries from government and education to electronics and food and beverage.
How the Fake Installer Attack Works
What makes this campaign especially dangerous is that it targets both technical and non-technical users. Developers who work with command-line tools are often comfortable copying setup commands from documentation pages, and non-technical users are equally likely to follow on-screen steps that look official. The attackers crafted these fake pages to closely resemble a real Claude installation guide, making the deception very hard to spot.
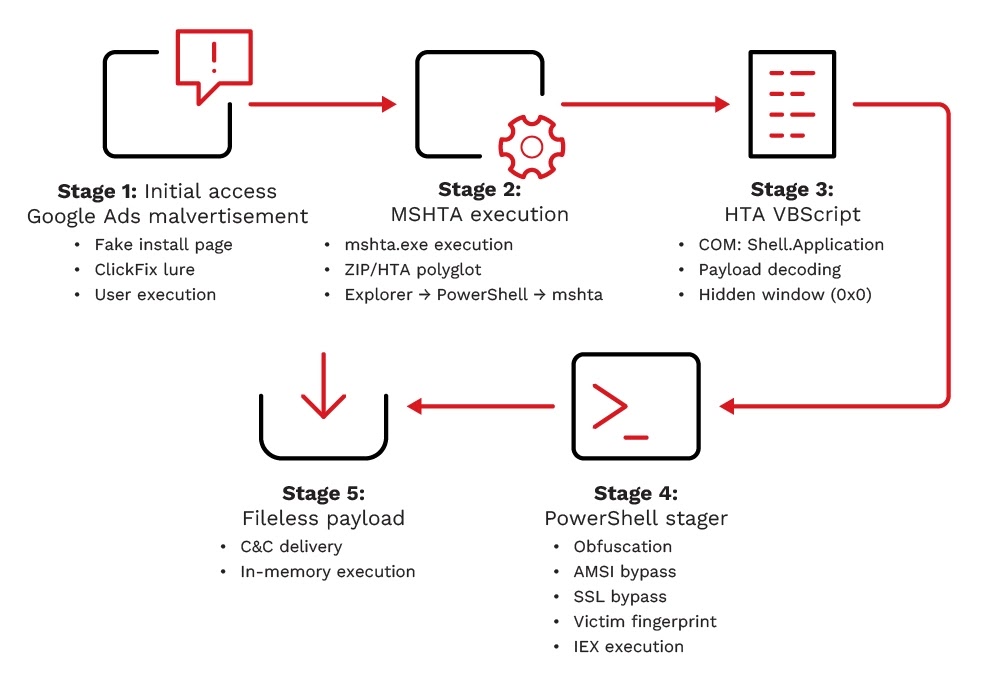
The threat goes beyond a single download. After the user runs the malicious command, the infection unfolds across multiple stages, each designed to evade detection and remain hidden. Trend Micro’s telemetry confirmed outbound network connections to attacker-controlled servers, and the indicators found align closely with those tied to RedLine Stealer campaigns from 2023.
The attack begins with a Google Ads placement that intercepts users searching for Claude Code. The fake landing page uses a technique called ClickFix, presenting an OS-specific command framed as a required installation step. On Windows, running the command triggers a hidden chain beginning with mshta.exe, a legitimate Windows tool that attackers commonly abuse to execute remote payloads.
The downloaded file, named claude.msixbundle, appears to be a genuine Microsoft package with valid Marketplace signatures, allowing it to pass basic security checks. Embedded inside is an HTA payload that silently executes a VBScript, with the window resized to zero pixels so nothing appears on screen.
That script launches obfuscated PowerShell commands through the SysWOW64 subsystem, bypassing detection by reconstructing the word “powershell” at runtime using split variables.
The stager generates a unique ID for the victim machine by hashing the computer name and username together. It uses this hash to build a custom command-and-control URL for each victim, fetching the final payload from a subdomain on oakenfjrod[.]ru. This per-victim URL approach makes bulk network-level blocking extremely difficult to execute.
Persistence, Data Theft, and RedLine Stealer Connections
Once the shellcode runs in memory, the malware establishes persistence by creating scheduled tasks, allowing it to survive reboots and keep running silently. Dynamic analysis showed the malware reaching out to external IP addresses, collecting browser data, and targeting e-wallet applications installed on the infected machine.
The indicators tied to this campaign match techniques and infrastructure previously linked to RedLine Stealer.
To reduce risk, organizations should block known malicious domains and IP addresses at the firewall and use DNS filtering to prevent users from reaching suspicious or newly registered domains. Legacy scripting tools like mshta.exe should be restricted wherever possible.
Users should also be trained to avoid running commands from sites reached through sponsored search results, to verify download pages against official vendor websites, and to rely on trusted package managers like npm, pip, brew, or winget rather than manual scripts from unknown sources.
Indicators of Compromise (IoCs):-
| Type | Indicator | Description |
|---|---|---|
| Domain | download-version[.]1-5-8[.]com | Malicious domain hosting the fake claude.msixbundle payload |
| Domain | oakenfjrod[.]ru | Attacker-controlled C&C domain; victim-unique subdomains used for Stage 4 payload delivery |
| URL | hxxps[://]download-version[.]1-5-8[.]com/claude[.]msixbundle | Download URL for the ZIP/HTA polyglot malicious package |
| URL | https://[nipple].oakenfjrod[.]ru/cloude-91267b64-989f-49b4-89b4-984e0154d4d1 | Victim-unique C&C URL used to fetch and execute the final in-memory payload |
| File Name | claude.msixbundle | Malicious payload disguised as a Claude AI installer; ZIP/HTA polyglot file |
| File Name | Claude.msixbundle.zip | Malicious archive containing obfuscated VBScript payload embedded in an HTML file |
| SHA1 | 811fbf0ff6b6acabe4b545e493ec0dd0178a0302 | Hash of the recovered Stage 5 payload file (content execution not confirmed) |
| SHA256 | 2f04ba77bb841111036b979fc0dab7fcbae99749718ae1dd6fd348d4495b5f74 | SHA256 hash of the Stage 5 payload |
| IP Address | 104[.]21[.]0[.]95 | Outbound C&C IP observed during dynamic analysis |
| IP Address | 185[.]177[.]239[.]255 | Outbound C&C IP observed during dynamic analysis |
| IP Address | 77[.]91[.]97[.]244 | IP address contacted over HTTPS port 443; TCP SYN requests observed; resolved to hosted-by[.]yeezyhost[.]net |
Note: IP addresses and domains are intentionally defanged (e.g., [.]) to prevent accidental resolution or hyperlinking. Re-fang only within controlled threat intelligence platforms such as MISP, VirusTotal, or your SIEM.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.








No Comment! Be the first one.