Bluekit Phishing Kit Automates 2FA Lures Domains Session
A newly identified phishing kit, dubbed Bluekit, is fundamentally changing how cybercriminals carry out phishing attacks by consolidating multiple attack capabilities within a single, easy-to-use...
A newly identified phishing kit, dubbed Bluekit, is fundamentally changing how cybercriminals carry out phishing attacks by consolidating multiple attack capabilities within a single, easy-to-use operator panel. This sophisticated tool, detailed in a recent analysis, automates key elements of credential theft campaigns, from deploying two-factor authentication (2FA) lures to managing malicious domains and facilitating session hijacking.
**
Rather than relying on separate tools stitched together from different sources, Bluekit gives attackers one centralized platform to manage everything from fake website creation to session hijacking.
For years, phishing kit operators had to buy a credential-harvesting page from one seller, a domain rotator from another, and an SMS gateway from a third.
That process required technical knowledge and time. Bluekit changes that model by bundling all of these capabilities into one dashboard, lowering the barrier for even less experienced threat actors to launch polished phishing campaigns.
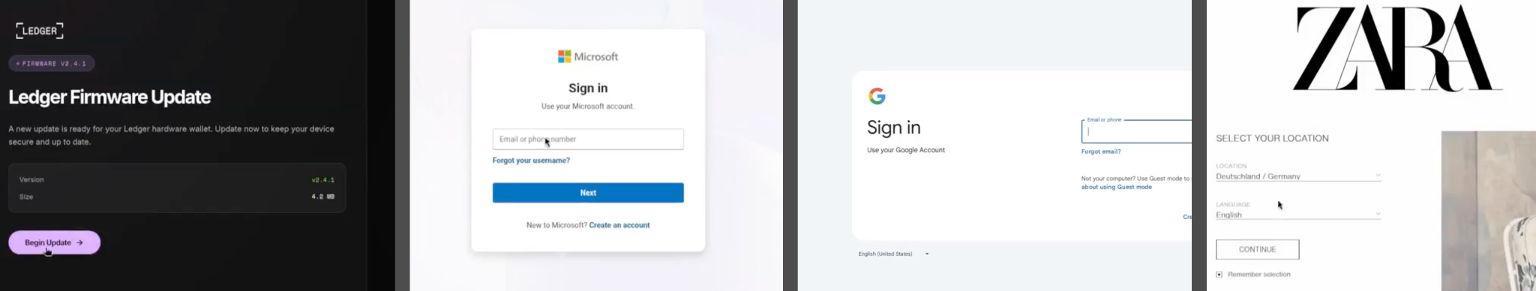
The kit advertises over 40 website templates, automated domain purchase and registration, two-factor authentication (2FA) support, spoofing, geolocation emulation, Telegram notifications, antibot cloaking, and optional add-ons like voice cloning and a mail sender.
Varonis Threat Labs researchers identified and analyzed Bluekit after gaining access to the kit and reviewing its internal structure.
The research team examined the operator dashboard, the site-creation flow, post-capture panels, and the built-in AI Assistant.
Their analysis revealed that the kit handles far more than a basic credential grab, with its panel surfacing session data, stored cookie dumps, and local storage content after a target logs in.
The templates reviewed by the team covered a wide range of services, including iCloud, Apple ID, Gmail, Outlook, Hotmail, Yahoo, ProtonMail, GitHub, Twitter, Zoho, Zara, and Ledger.
The impact of this kit is significant. Because Bluekit centralizes so many steps of the phishing workflow, attackers can now spin up convincing phishing pages, register domains, and monitor captured sessions without switching between tools or platforms.
The Telegram integration is set as the default exfiltration channel, meaning stolen credentials and session tokens are sent directly to an attacker-controlled chat in real time. This makes response time faster and tracing harder for defenders.
How Bluekit Hijacks Sessions After Login
The most concerning capability of Bluekit is not just its ability to steal passwords but what it does after a victim submits their credentials.
Session hijacking is built directly into the kit’s core design. In the “Mammoth Details” view examined during the research, Bluekit tracked session state, stored repeated dumps of cookies and local storage, and kept a live view of what the target saw after logging in.
This means that even if a victim has 2FA enabled on their account, Bluekit is designed to capture the session tokens that are generated after a successful 2FA verification, effectively bypassing that layer of security entirely.
The site-edit configuration panel, exposed login-detection actions, redirect behavior, anti-analysis checks, spoofing options, and device filters from a single screen.
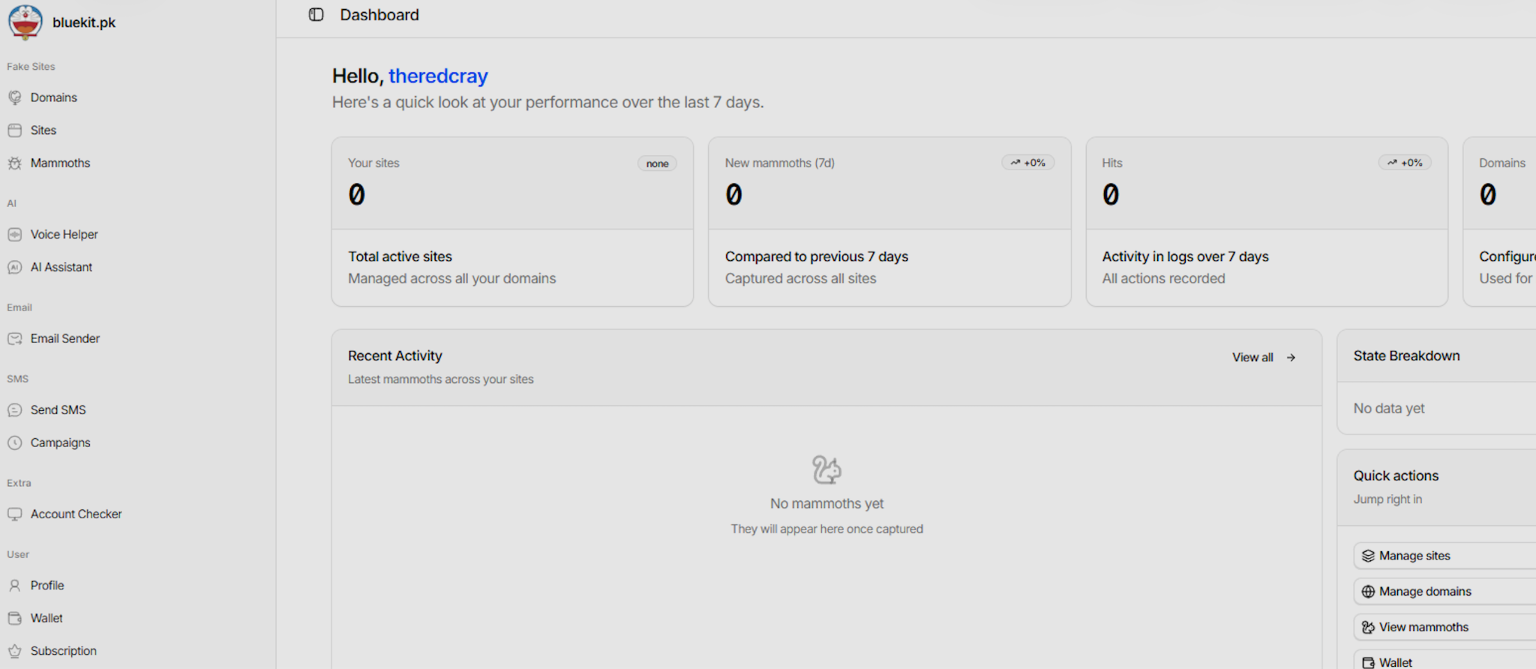
Operators could also configure proxy settings and site-level checks tied to how sessions were handled post-login.
This level of granular control is what makes Bluekit stand out from older, simpler phishing kits that only collected a username and password.
By managing the entire session lifecycle, attackers can take over accounts even when modern authentication controls are in place.
Bluekit also features an AI Assistant with its own panel inside the dashboard, offering multiple AI model options, including an abliterated Llama model as default, alongside listed options for GPT-4.1, Claude Sonnet 4, Gemini, and DeepSeek variants.
During testing, the AI component generated structured phishing campaign drafts, though it still required manual cleanup before campaigns were usable.
Organizations are strongly advised to enforce phishing-resistant authentication methods such as hardware security keys, as session token theft can bypass standard 2FA.
Security teams should monitor for unusual login locations, unexpected session token reuse, and cookie injection attempts.
Employees should be regularly trained to recognize lookalike login pages, and network teams should enable strict domain reputation filtering to block newly registered phishing domains before they reach end users.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.