Ransomware Detection With Windows Minifilter by Intercepting File
Ransomware continues to inflict significant financial damage on organizations globally. A key technology for robust monitoring within Windows environments is the minifilter driver. By sitting...
Ransomware continues to inflict significant financial damage on organizations globally. A key technology for robust monitoring within Windows environments is the minifilter driver.
By sitting directly in the file system I/O pipeline, a minifilter can observe, intercept, and even block malicious file operations in real time, providing a crucial early-warning layer for endpoint detection and response (EDR) systems.
Security researcher 0xflux has unveiled a proof-of-concept (POC) Windows minifilter driver for real-time ransomware detection. It intercepts file system events to flag suspicious behaviors like rapid file writes and renames to known malicious extensions.
The Filter Manager, a kernel-mode component, provides a rich API for minifilter drivers, eliminating the need to build legacy filter drivers from scratch.
Minifilter drivers register their I/O operation callbacks with the Filter Manager, which invokes them in order of altitude, ensuring deterministic layering when multiple filters are loaded.
A minifilter begins life like any kernel driver, with a DriverEntry function. Instead of the typical driver setup, it uses the Flt function family FltRegisterFilter, FltStartFiltering to register itself and declare callback functions for specific I/O request packets (IRPs).
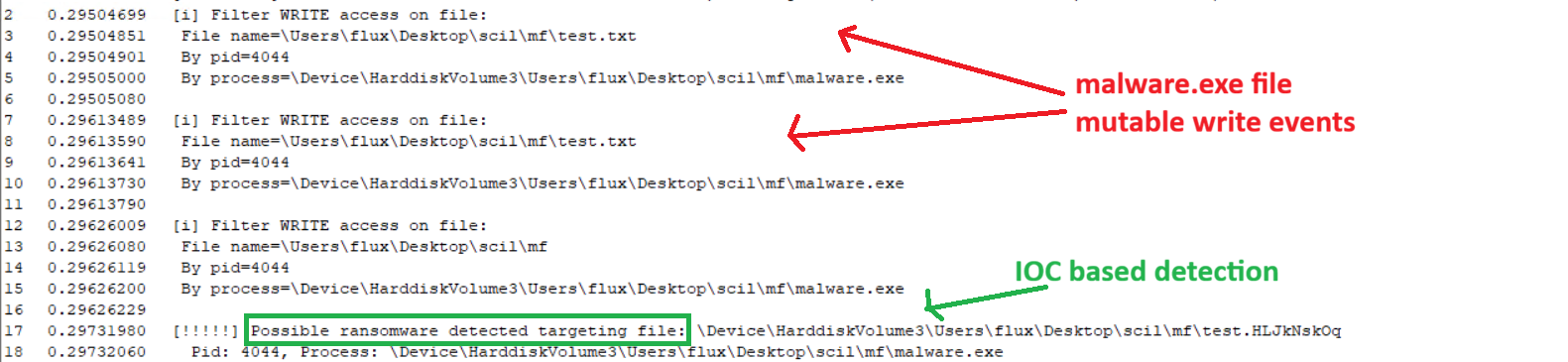
PostOperationSetInformation handles renames, filtering for FileRenameInformation classes. It retrieves normalized file names via FltGetFileNameInformation and FltParseFileNameInformation, then scans extensions against a list like L”.HLJkNskOq” from LockBit IOCs.
A match triggers alerts to a user-mode engine for further checks, such as file entropy analysis, a hallmark of encrypted data. Process details, including PID via PsGetProcessId and image name via SeLocateProcessImageName, are logged for correlation.
For writes, PostOperationCreate filters access masks like FILE_WRITE_DATA or FILE_APPEND_DATA. This flags processes seeking mutable file access, signaling potential encryption prep. Pre-operation callbacks simply return FLT_PREOP_SUCCESS_WITH_CALLBACK to enable post-handling without blocking.
The C-based driver, hosted on GitHub under Sanctum/fs_minifilter, includes safety checks for production use. A Rust simulator mimics ransomware: opens test.txt, writes junk bytes, and renames it to test.HLJkNskOq. When loaded, the driver detects and logs these events, proving efficacy against LockBit-like behavior.
Beyond extensions, the approach tracks event volume: one process hitting multiple directories signals an outbreak. Inspection of file type correlations and entropy enhances fidelity.
Future enhancements include user-mode collectors for process trees, partial file reads, and rate-limiting detections (e.g., high-entropy changes per second). Freezing suspect threads could buy response time.
This POC from Flux aligns with trends in behavioral EDR, outperforming signature-based AV against fileless or polymorphic threats.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.