Telegram Phishing Steals Full User Sessions via Auth
A sophisticated Telegram phishing campaign has resurfaced, signaling a significant evolution in the methods threat actors use to compromise user accounts. Unlike traditional credential harvesting,...
A sophisticated Telegram phishing campaign has resurfaced, signaling a significant evolution in the methods threat actors use to compromise user accounts.
Unlike traditional credential harvesting, this operation does not rely on cloning login pages to steal passwords but instead manipulates the platform’s legitimate authentication infrastructure.
By integrating directly with Telegram’s official login workflows, the attackers can bypass standard security filters and obtain fully authorized user sessions without raising immediate alarms.
The attack vectors are designed to minimize user suspicion by mimicking routine security checks and verification procedures.
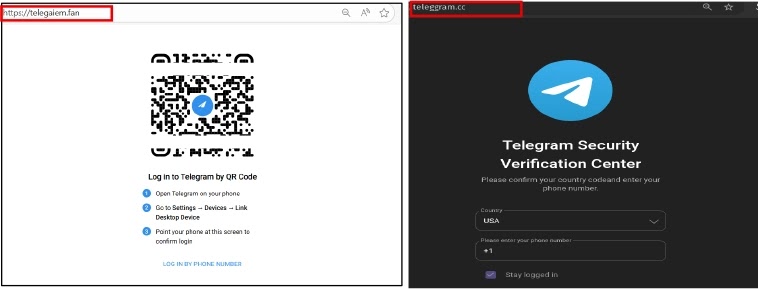
Victims are presented with fraudulent login interfaces that support both QR-code scanning and manual phone number entry.
These interfaces are hosted on ephemeral domains that closely resemble legitimate Telegram branding.
When a user interacts with these elements, they are not sending data to a hacker’s database but are inadvertently triggering a real login request initiated by the attacker’s device.
Cyfirma analysts identified this malware after observing its unique ability to frame authorization prompts as security verifications.
The researchers noted that this method significantly increases victim compliance while reducing detectable anomalies.
Once the user approves the request on their mobile device, believing they are verifying their identity, the attackers gain immediate, persistent access to the account.
This allows them to monitor communications and launch secondary attacks against the victim’s contacts without alerting the user through typical suspicious login warnings or requiring exploit-based access.
Dynamic Infrastructure and API Abuse
The technical sophistication of this campaign is evident in its use of dynamic backend configurations to evade detection.
Rather than hardcoding phishing logic into the frontend HTML, the site retrieves runtime instructions from a centralized server via cross-origin API requests.
This JSON response delivers attacker-controlled Telegram API credentials, such as the api_id and api_hash, along with localized language data to render the login interface.
This configuration-driven design allows the operators to rapidly rotate domains while maintaining consistent authentication logic across globally distributed targets.
The phishing pages also display misleading system messages, instructing users to click “Yes” on the in-app notification to “verify” their account.
By shifting the decisive action to the trusted Telegram app interface, the campaign successfully masks the malicious nature of the session binding process.
To mitigate these risks, users must exercise extreme caution with in-app authorization prompts.
Never approve a login request unless you personally initiated it, even if the prompt claims to be a security check or unusual activity review.
It is essential to avoid scanning QR codes from unfamiliar websites and to regularly audit active sessions within Telegram’s “Devices” settings.
Finally, enabling Two-Step Verification adds a critical layer of defense, preventing unauthorized session creation by requiring a secondary password even if a user is tricked into approving the initial prompt.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.