APT-Q-27 Stealth Attack on Corporate Targeting Environments
In mid-January 2026, a highly sophisticated cyber campaign surfaced, specifically targeting financial institutions. Its key characteristic was the ability to infiltrate corporate environments without...
In mid-January 2026, a highly sophisticated cyber campaign surfaced, specifically targeting financial institutions. Its key characteristic was the ability to infiltrate corporate environments without triggering standard security alerts.
The attack was notable for its extreme stealth, as neither the end-users nor conventional endpoint protection controls raised any immediate alarms during the initial intrusion.
This low-noise approach allowed the threat actors to bypass traditional defenses completely, posing a severe risk to organizations where data integrity and operational trust are non-negotiable.
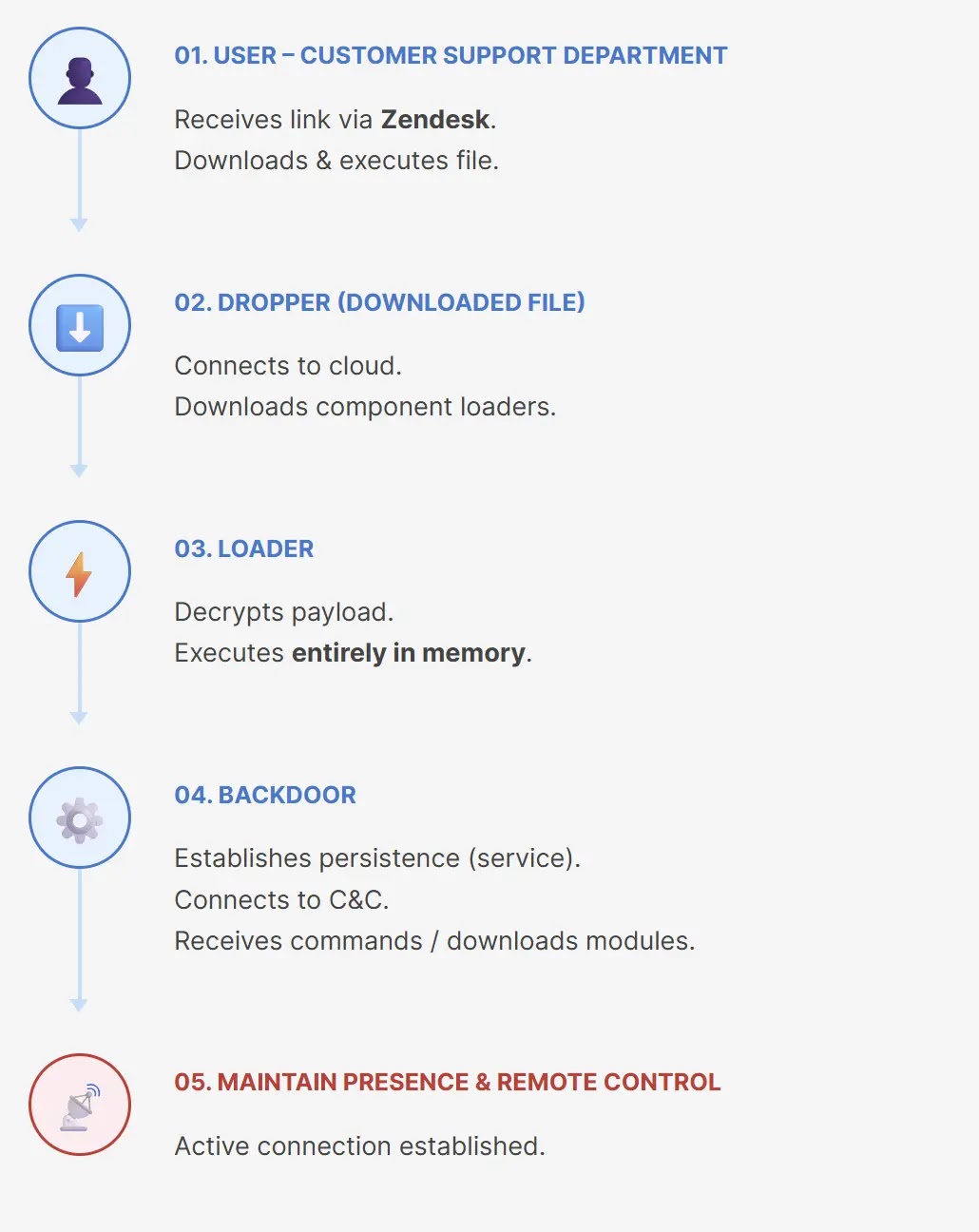
The infection vector was successfully traced back to a corporate customer support department, where a user interacted with a malicious link received through a Zendesk ticket.
The URL was crafted to appear as a harmless image file, but it actually facilitated the download of an executable masking as a “.pif” file.
Because Windows operating systems often hide known file extensions by default, the malicious file appeared to be a legitimate image or document.
This simple but effective social engineering tactic significantly reduced user suspicion and allowed the malware to bypass initial reputation-based checks.
CyStack analysts identified the malware following a deep forensic investigation into the affected workstation.
They noted that the campaign’s command-and-control infrastructure and modular backdoor design shared significant overlaps with previous activities attributed to the APT-Q-27 group, also known as GoldenEyeDog.
The malware employed a valid, albeit revoked, digital signature from “Portier Global Pty Ltd.”
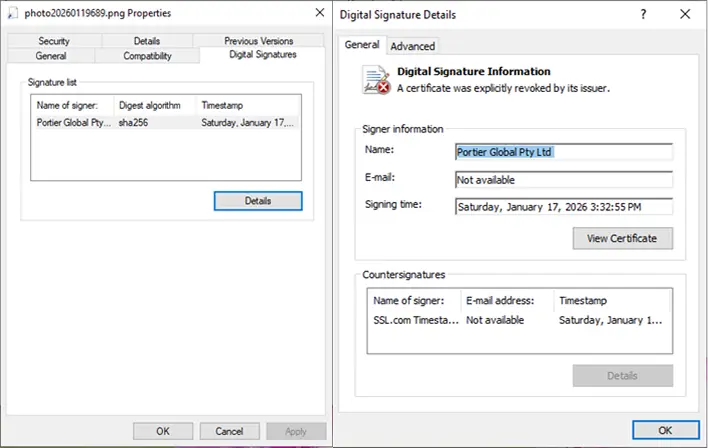
The presence of a valid timestamp on the certificate meant that Windows continued to trust the file despite the revocation, allowing it to circumvent SmartScreen filters and execute on the target system without blocking.
Evasion via DLL Sideloading
A critical aspect of this campaign is its advanced evasion techniques, specifically its reliance on DLL sideloading and in-memory execution.
Upon infection, the dropper establishes a staging directory designed to mimic a Windows Update cache path, effectively blending in with legitimate system folders.
Inside this hidden directory, a signed, benign executable is used to load a malicious DLL file named crashreport.dll.
This technique allows the attackers to execute their final payload entirely within the computer’s memory, avoiding the creation of detectable files on the hard drive.
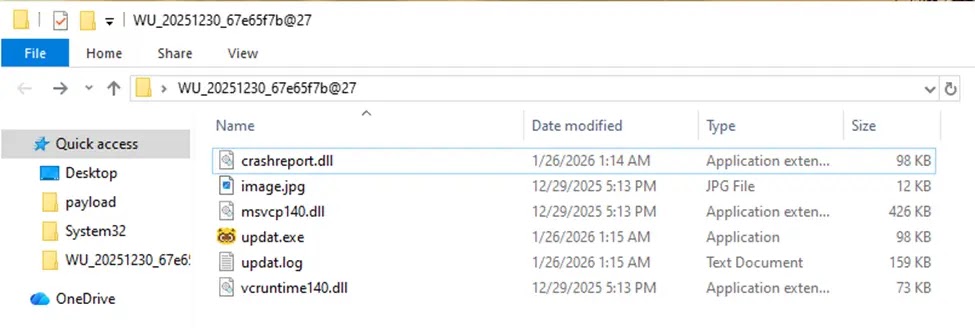
By operating within the context of a trusted process, the backdoor can receive commands and download additional modules while remaining invisible to many file-based scanning tools.
To defend against such stealthy intrusions, CyStack recommends that enterprises prioritize proactive threat hunting focused on detecting abnormal process behaviors like unexpected DLL loading.
It is essential to maintain incident response readiness to rapidly isolate affected systems before lateral movement occurs.
Additionally, organizations should deploy behavior-based endpoint protection rather than relying solely on signatures and leverage contextual threat intelligence to identify campaign-specific indicators.
Finally, reviewing non-traditional attack surfaces, such as support ticketing systems where social engineering attacks are increasingly common, is crucial for closing security gaps.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.