RenEngine Loader Bypasses Security Controls via Stealth
A new HijackLoader variant has emerged, incorporating advanced anti-analysis modules designed to bypass security controls. These capabilities include checks for GPUs, hypervisor names, and VM-linked...
A new HijackLoader variant has emerged, incorporating advanced anti-analysis modules designed to bypass security controls. These capabilities include checks for GPUs, hypervisor names, and VM-linked MAC addresses.
Together, RenEngine and HijackLoader form a dual-loader setup that helps the operators swap payloads quickly as defenses change.
A typical run starts when a user executes the pirated installer, then RenEngine decrypts and launches the second stage.
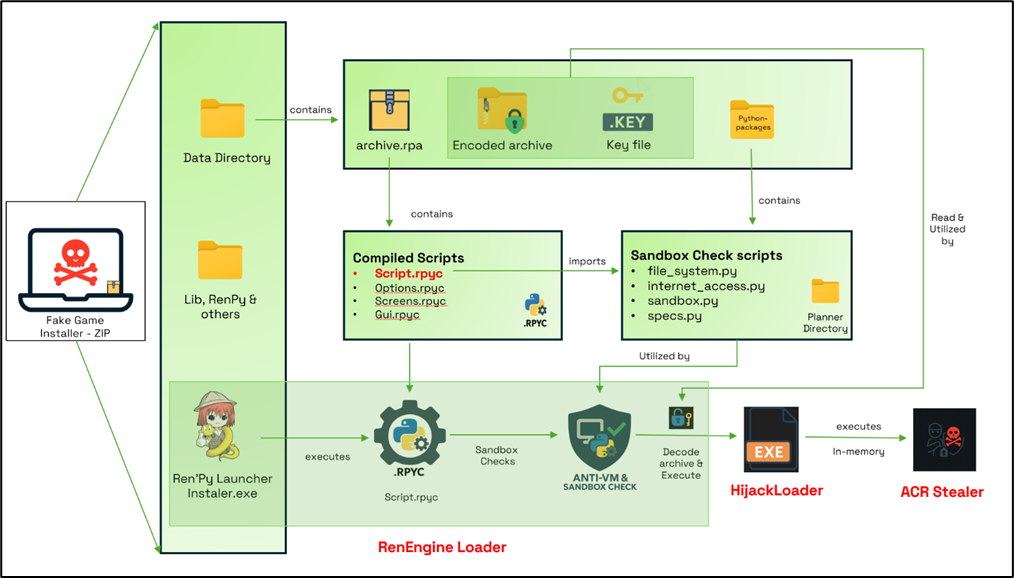
HijackLoader is then introduced through DLL side-loading and module stomping, and the final payload observed in this chain is ACR Stealer.
ACR Stealer is built to collect browser passwords and cookies, crypto wallet data, and other system details, then send it to attacker infrastructure. Some chains have also delivered other stealers, such as Vidar.
Infection mechanism inside Ren’Py
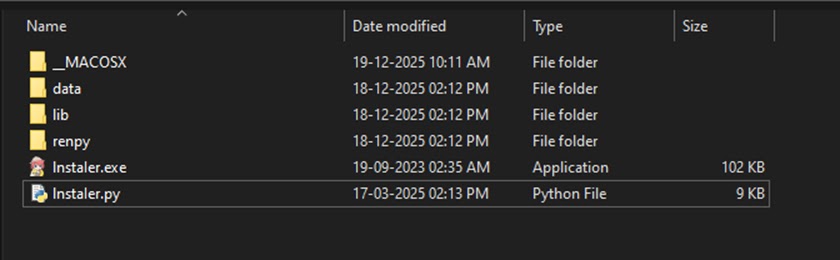
Infection begins in the game folder, where Instaler.exe is a real Ren’Py launcher but is abused to run a compiled script from archive.rpa.
The build strips plain .rpy files and keeps only .rpyc, reducing visibility during scans.
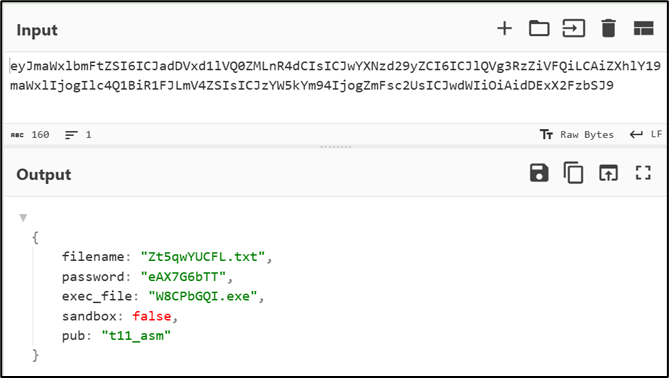
Next, RenEngine reads a local .key file, Base64-decodes it into JSON, and uses the password value to XOR-decrypt an embedded archive before running the next executable.
When sandbox checks are enabled, the loader scores the environment and exits silently if it believes it is running in a virtual machine.
For defense, treat piracy installers and mods as high risk and block them where possible.
Watch for Ren’Py launchers unpacking RPA content, Base64/XOR staging, and aggressive VM checks, then correlate with suspicious DLL side-loading and sudden credential theft traffic across endpoints today.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.