China-Nexus Hackers Hijacking Linux-Based Devices to Manipulate
The emergence of “DKnife,” a sophisticated surveillance and attack framework, now poses a significant threat to network security. Attributed to China-nexus threat actors, this malicious toolset...
The emergence of “DKnife,” a sophisticated surveillance and attack framework, now poses a significant threat to network security.
Attributed to China-nexus threat actors, this malicious toolset specifically targets Linux-based routers and edge devices.
By compromising these critical network gateways, attackers can establish a persistent foothold within a target’s infrastructure, allowing them to monitor data flow and manipulate network traffic with high precision.
The malware operates as a fully featured Adversary-in-the-Middle (AitM) framework, designed to inspect network packets in real-time.
It has been active since at least 2019 but remained largely undetected until recently.
The framework is composed of multiple components that work together to hijack legitimate user requests, such as software updates, and replace them with malicious content.
This allows the attackers to install backdoors on devices connected to the compromised network without the user’s knowledge.
Cisco Talos analysts identified the DKnife malware while investigating the distribution of the DarkNimbus backdoor. Their analysis revealed that DKnife is not just a passive monitoring tool but an active attack platform.
It is capable of intercepting traffic destined for specific services, particularly those popular among Chinese-speaking users, and injecting malicious payloads.
This discovery highlights the evolving tactics of threat actors who are increasingly moving their operations to edge devices to evade traditional endpoint security measures.
The impact of a DKnife infection is far-reaching. Once a router is compromised, every device connected to it becomes a potential target.
The malware can selectively disrupt traffic from antivirus products, preventing them from updating or communicating with their servers.
Furthermore, it can harvest sensitive user data, including credentials and device identifiers, effectively turning the network gateway into a comprehensive espionage tool.
The Mechanics of Traffic Hijacking and Malware Delivery
At the core of DKnife’s offensive capabilities is its ability to seamlessly hijack binary downloads.
The framework employs a complex deep packet inspection (DPI) engine that constantly monitors network traffic for specific types of requests, such as Android application updates or Windows executable downloads.
When a matching request is detected, the malware intervenes before the request reaches the legitimate server.
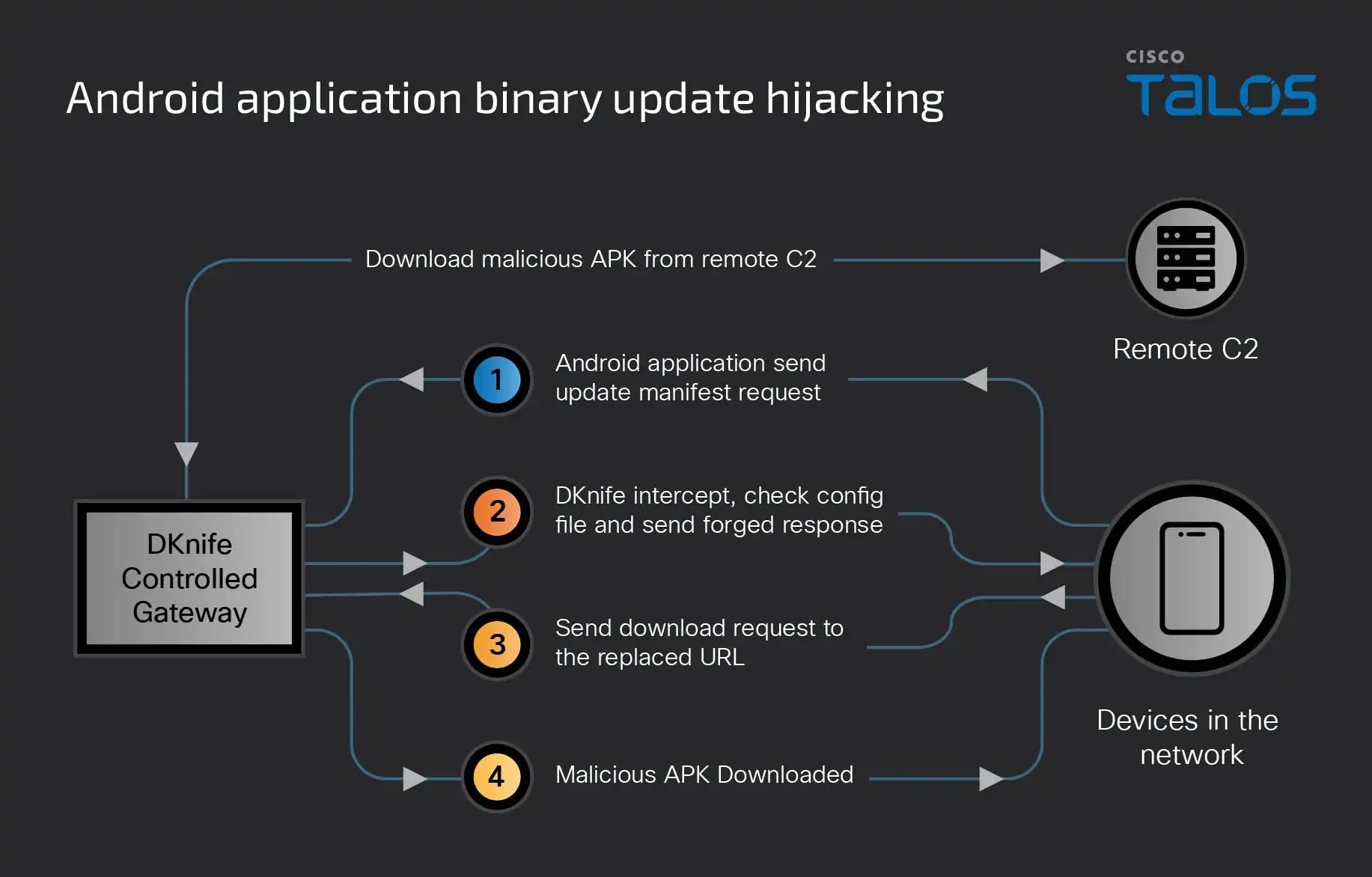
This complete process involves several distinct steps. The compromised gateway intercepts the initial update manifest request and checks it against a local configuration file.
If a match is found, DKnife sends a forged response back to the victim’s device. This response redirects the download to a malicious URL hosted on a virtual internal network created by the malware itself.
This internal network is managed by a component called yitiji.bin, which creates a bridged interface to route the attacker’s traffic.
By keeping the malicious delivery within this virtual local area network, the attackers avoid IP address conflicts and reduce the risk of detection by external network monitoring tools.
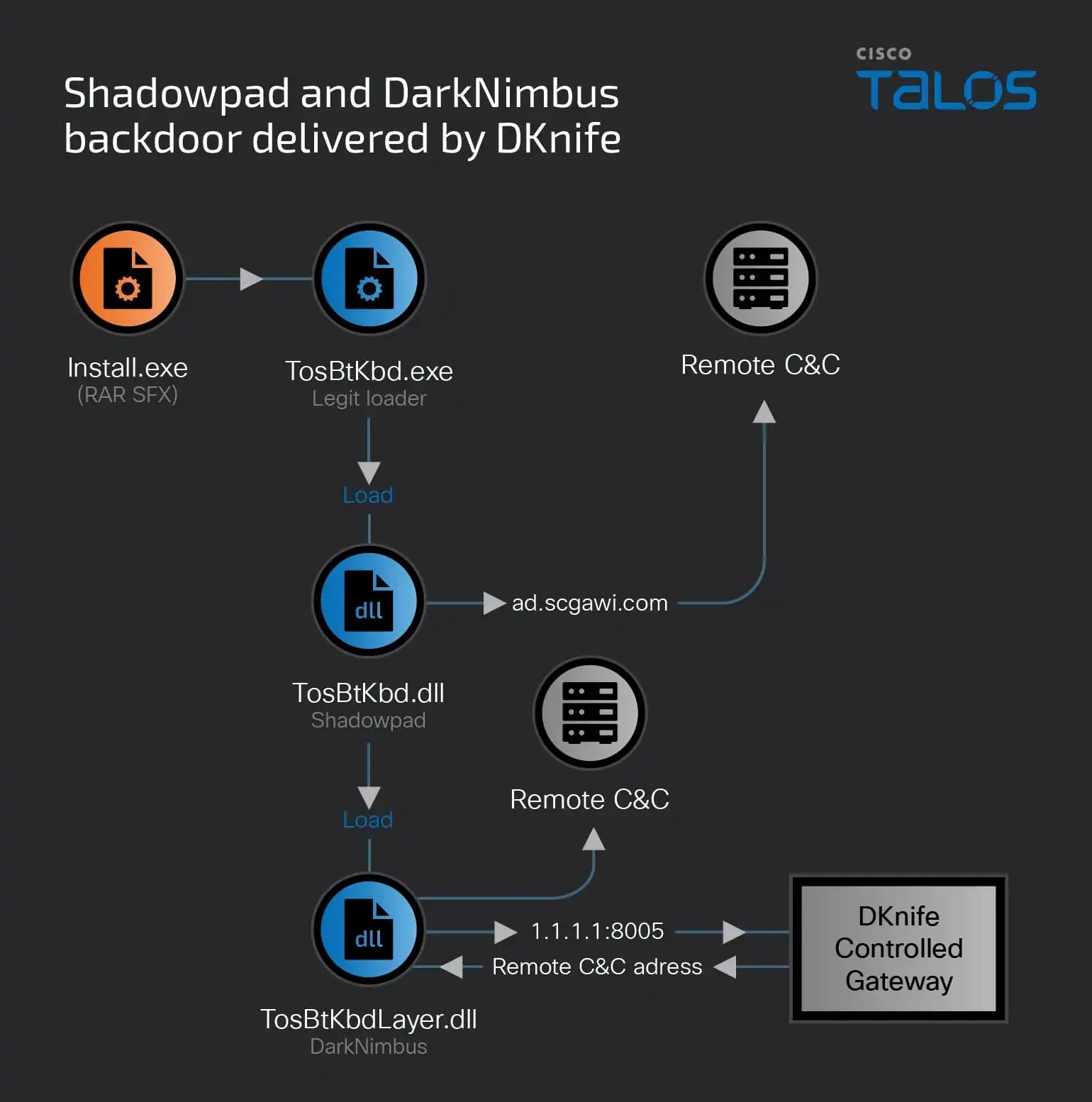
This stealthy mechanism ensures that the victim believes they are downloading a legitimate update, while in reality, they are installing backdoors like ShadowPad or DarkNimbus, effectively granting the attackers full control over the endpoint device.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.