Phishing and OAuth Token Flaws Lead to Full Microsoft 365 Compromise
Internal services in many cloud environments authenticate using OAuth tokens. A common vulnerability arises when applications, configured to display verbose errors for debugging, respond to malformed...
Internal services in many cloud environments authenticate using OAuth tokens. A common vulnerability arises when applications, configured to display verbose errors for debugging, respond to malformed requests by inadvertently dumping these sensitive authentication tokens alongside stack traces.
The Mechanics of Token Hijacking
The technical core of this compromise relies on the mishandling of OAuth 2.0 bearer tokens within the application context.
When an attacker intentionally submits incomplete or malformed JSON payloads to the API, the system fails to degrade gracefully. Instead of a generic error, it returns a comprehensive debugging log to the client.
This log contains the active JSON Web Token (JWT) used by the service to communicate with the Microsoft Graph API.
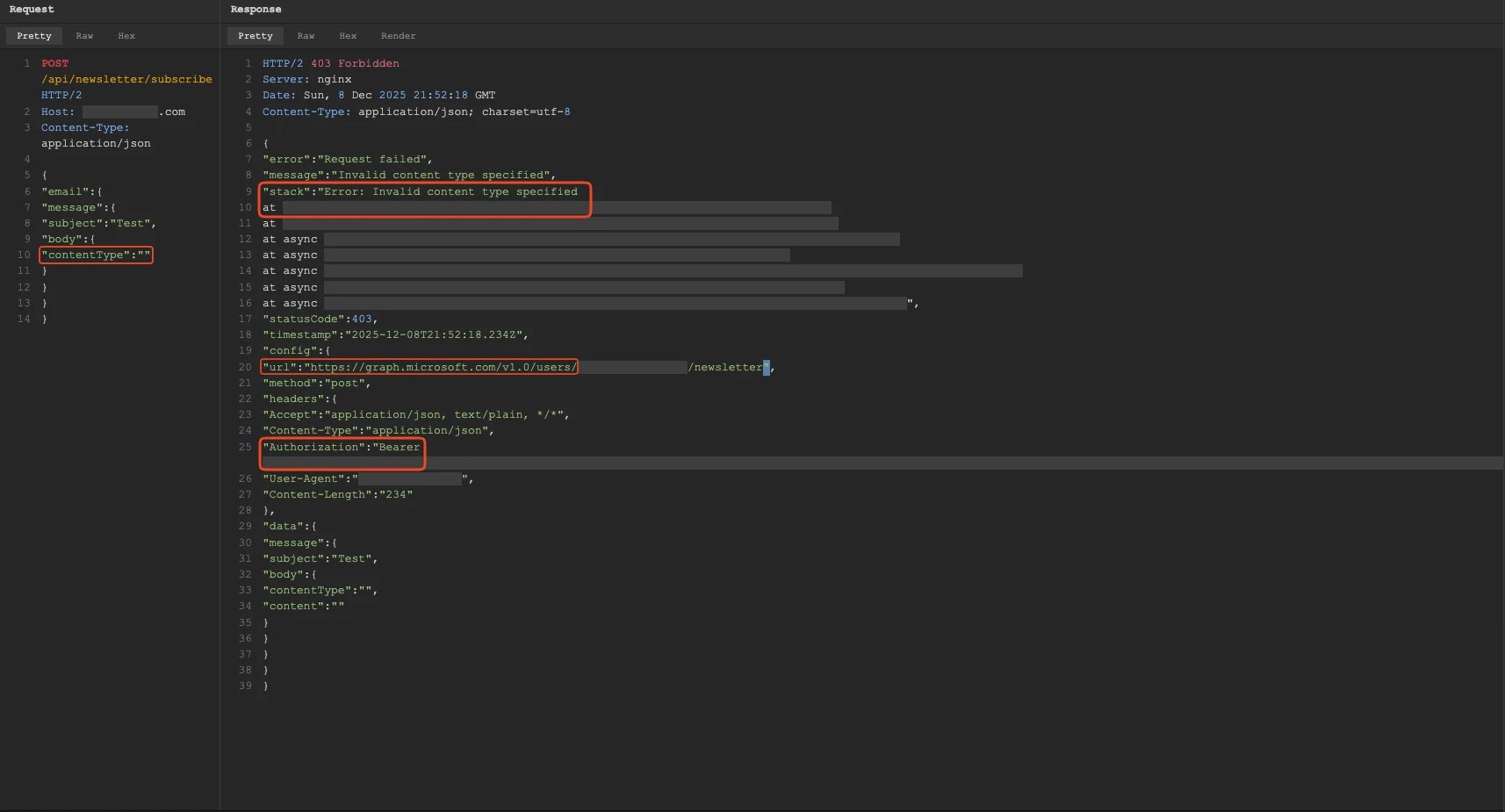
Once extracted, these tokens provide immediate, authenticated access to organizational resources without requiring user credentials or triggering typical login alerts.
Depending on the token’s scope, adversaries can silently exfiltrate SharePoint documents, access sensitive Teams chat history, or modify Outlook calendars.
This persistent foothold allows them to pivot to broader Azure infrastructure if the token holds sufficient privileges. By repeatedly triggering the error condition, attackers can harvest fresh tokens, maintaining access even as sessions expire.
To effectively mitigate these risks, security teams must enforce strict input validation on all public APIs, ensuring they accept only the absolute minimum necessary parameters.
Furthermore, organizations should ensure that production environments are configured to return generic error messages, suppressing detailed debug information that could inadvertently leak internal system state or active credentials.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.