Microsoft & Authorities Dismantle RedVDS BEC Attack Chain
Microsoft and international law enforcement, collaborating in a joint operation, have dismantled a business email compromise (BEC) attack chain. This chain was powered by the RedVDS fraud engine....
Microsoft and international law enforcement, collaborating in a joint operation, have dismantled a business email compromise (BEC) attack chain. This chain was powered by the RedVDS fraud engine.
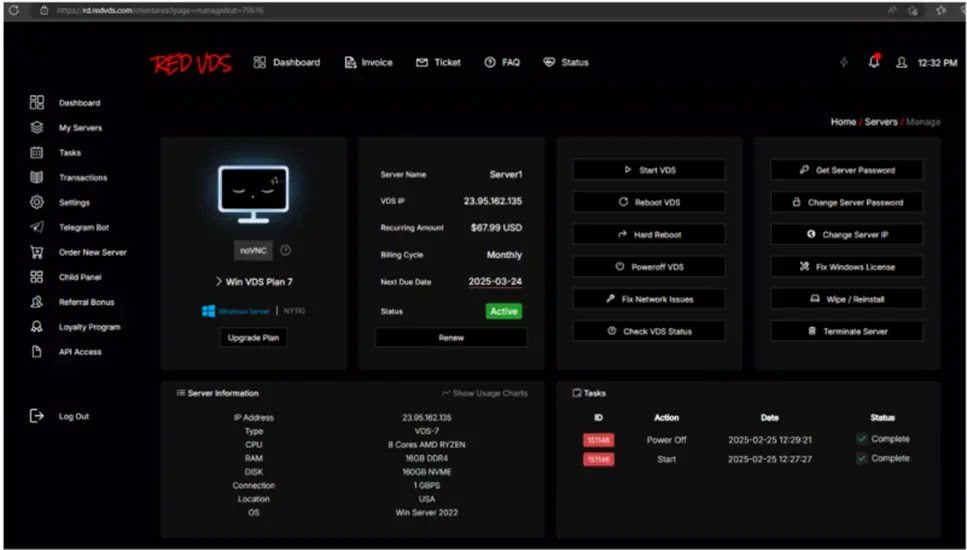
RedVDS operated as a low‑cost “cybercrime subscription” platform, giving criminals disposable virtual machines that looked like normal Windows systems on the internet.
Using these rented hosts, threat actors sent huge waves of phishing emails, hosted fake portals, and staged payment diversion schemes against companies in finance, real estate, healthcare, and manufacturing.
The attack chain was simple but very effective. Criminals first used RedVDS virtual machines to send targeted phishing emails that harvested credentials from Microsoft 365 and other mail platforms.
Once they gained mailbox access, they quietly watched real threads between vendors, clients, and internal teams, waiting for invoices, wire transfers, or closing instructions.
At the right moment, they injected fake replies with new bank details, routing large payments to accounts they controlled.
Microsoft analysts identified that RedVDS amplified this fraud by combining high‑volume infrastructure with AI tools that generated convincing email text, fake voice messages, and even deepfake videos.
On peak days, more than 2,600 RedVDS virtual machines sent around one million phishing messages to Microsoft customers alone, helping criminals compromise or abuse access to over 191,000 organizations worldwide.
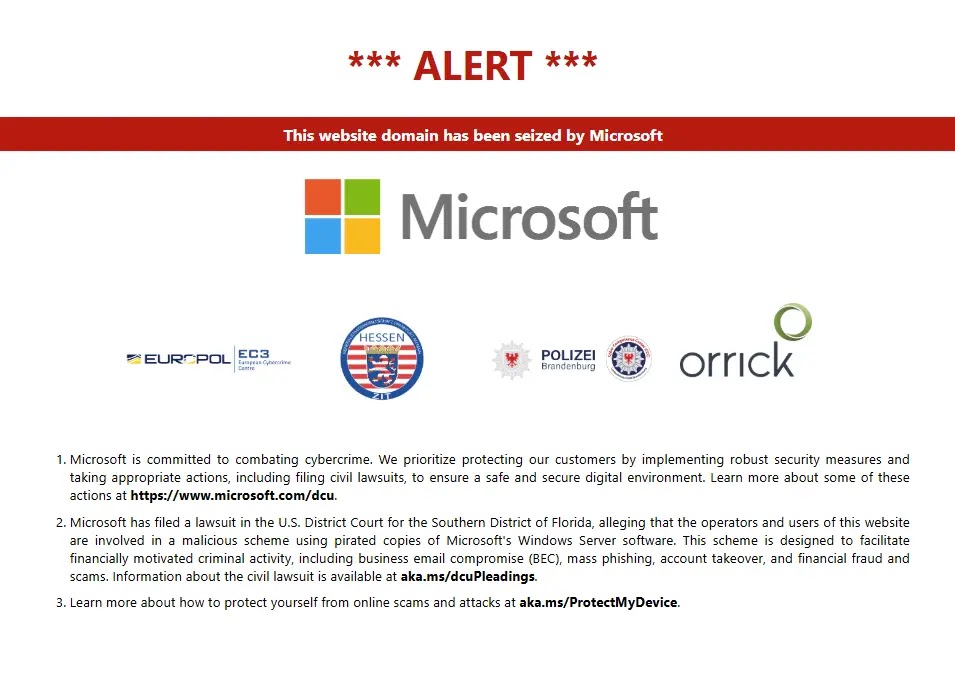
The coordinated takedown seized RedVDS domains, disrupted its payment channels, and removed a core pillar of this fraud ecosystem.
Investigators also tracked RedVDS use in real estate payment diversion, where hijacked mailboxes for agents and title firms were used to send fake closing instructions.
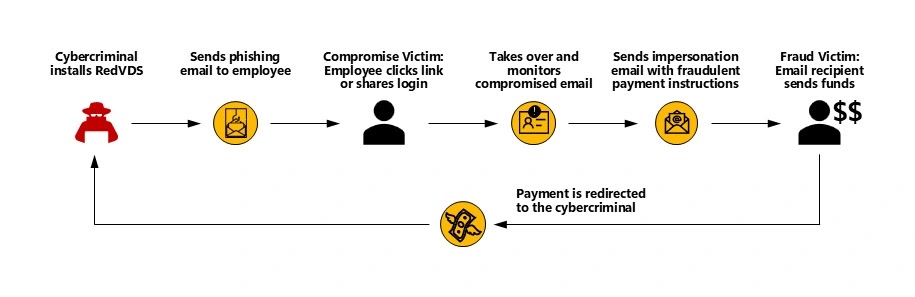
In many cases, victims wired their life savings to mule accounts within minutes of receiving the spoofed message.
How the RedVDS BEC Chain Operated
At a technical level, the BEC chain followed a repeatable script. Threat actors created or rented a RedVDS instance, deployed basic tooling, and pivoted into live mailboxes using stolen credentials.
A common pattern involved scripted login checks and inbox scans:-
for user in target_users:
if login(user.email, user.passwd, proxy=redvds_host):
for msg in inbox.search("invoice OR payment OR wire"):
if "upcoming" in msg.body.lower():
mark_as_watchlist(msg.thread_id)Once a payment thread was flagged, the actor crafted a reply from the compromised account, often reusing real signatures and footers:-
fake_reply = build_reply(original_thread,
body=new_bank_instructions,
from_account=compromised_mailbox)
send(fake_reply, via=redvds_host)Microsoft researchers noted that this structured playbook, combined with disposable RedVDS nodes, made the fraud easy to scale and hard to trace.
The recent operation shows that targeting shared crime infrastructure, not just single accounts, is key to shrinking the global BEC attack surface.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.








No Comment! Be the first one.